Mark Threats as a False Positive
Threat Protection works best when users actively work within the platform to resolve anomalies and threats. The information you provide to resolve threats trains Threat Protection on how to identify threats within your organization. To get a better result, your organization should resolve threats and anomalies on a regular basis. If the threat represents unusual behavior that does not indicate a security incident (for example, an employee who has a new project that requires an unusual number of record downloads), mark the anomaly as a false positive. Reports of false positives improve anomaly detection.
A security response team can mark threats as false positive, and record the results of the investigation into Threat Protection.
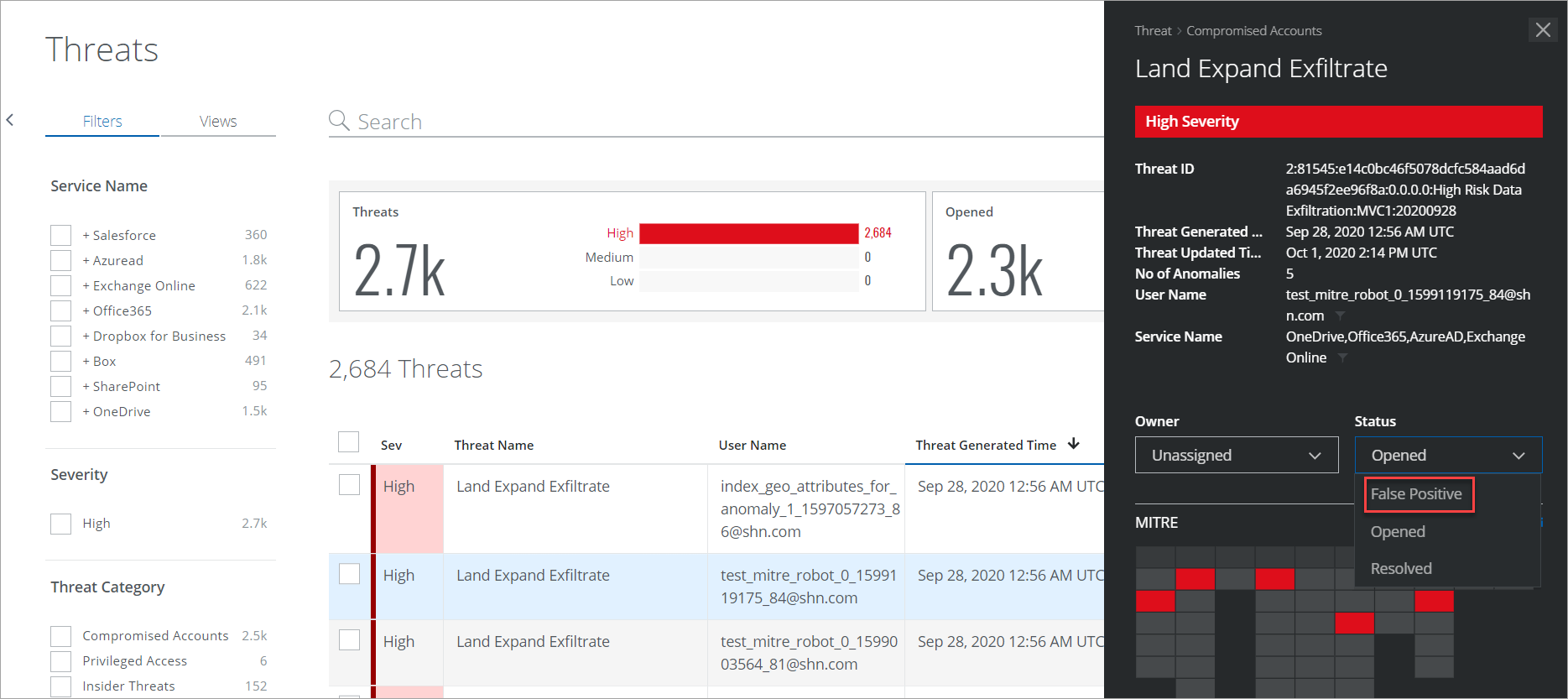
To Mark a Threat as a False Positive:
- Go to Incidents > Threats.
- In the Threats table, select the threat you want to mark as a false positive.
- In the Threat Cloud Card, select the Status as False Positive to remove the threat from the Threats list.
Once updated, a successful message displays at the bottom of the page.
IMPORTANT: This action cannot be undone.
