Proxy Configuration for Cisco WSA (Legacy)
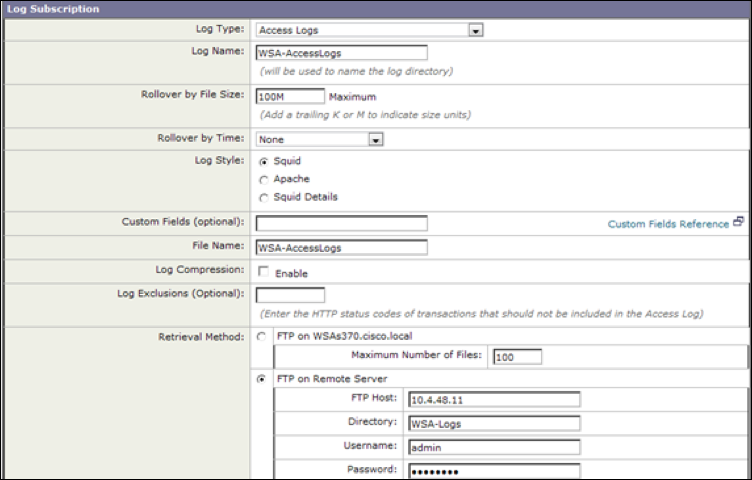
A log subscription is an appliance configuration that specifies the type of log file to create, the log file name, and the method of retrieving the log file. Skyhigh CASB works best with the W3C Access Log type.
To configure log file subscriptions, use the Cisco System Administration > Log Subscriptions page.
Add and Edit Log Subscriptions
To add or edit a log subscription perform these steps:
- Go to System Administration > Log Subscriptions.
- To add a log subscription, click Add Log Subscription. Or, to edit a log subscription, in the Log Name field, click the name of the log file. The New Log Subscription page or Edit Log Subscription displays.
- From the Log Type field, select the type of log to associate with this subscription. Choose W3C Access Log.
- In the Log Name field, enter a name for the log subscription. This name is used for the directory on the appliance that will contain the log file.
- Choose the fields you want to include in the W3C access log. Select a field in the Available Fields list, or enter a field in the Custom Field box and click Add.
- To edit the fields in the Selected Log Fields list:
- The order of the fields in the list determine the order of fields in the W3C access log file. To change the order, use the Move Up and Move Down buttons.
- To remove a field, in the Select Log Fields list, select it and click Remove.
- You may enter multiple user-defined fields in the Custom Fields field and add them simultaneously, as long as each entry is separated by a new line (press Enter) before you click Add.
- Add these fields:
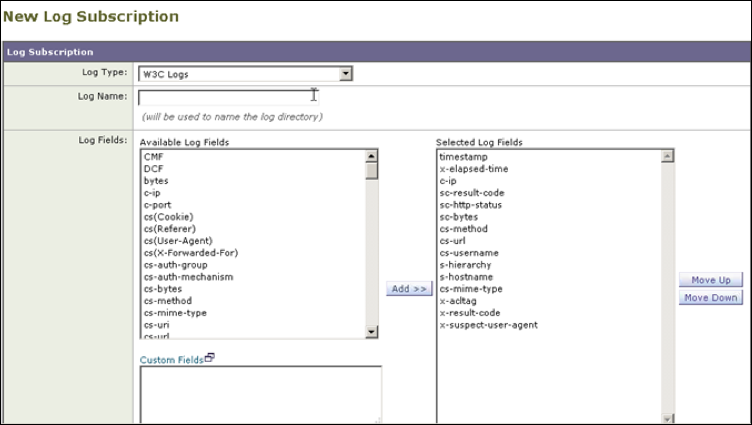
- c-ip %a Client IP Address.
- cs(User-Agent) %u User agent. This field is written with double-quotes in the access logs.
- cs-byte s %q Request size (headers + body).
- cs-mime-type %c Response body MIME type. This field is written with double-quotes in the access logs.
- cs-url %Y The entire URL.
- cs-username %A Authenticated user name. This field is written with double-quotes in the access logs.
- s-hostname %d Data source or server IP address.
- s-ip %k Data source IP address (server IP address).
- sc-bytes %s Response size (header + body).
- sc-http-statusß %h HTTP response code.
- sc-result-code %w Result code For example: TCP_MISS, TCP_HIT.
- sc-result-code-denial %W Result code denial.
- timestamp %t Timestamp in UNIX epoch.
- In the File Name field, enter a name for the log file.
- In the Maximum File Size field enter the maximum possible file size of the log file in bytes. After the number, enter the appropriate letter:
- G for Gigabytes
- M for Megabytes
- K for Kilobytes
- In the Log Compression field, select Enable to compress log files after they have been rolled over.
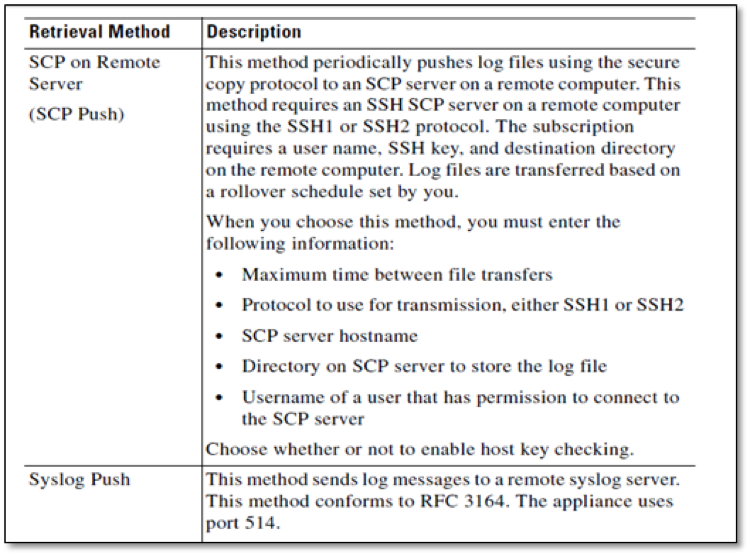
- In the Retrieval Method field, select a method to retrieving the log file from the appliance.
- Click Submit to commit your changes.
- If you chose SCP as the retrieval method, the appliance displays an SSH key you must add to the SCP server host.
Configure Log Retrieval
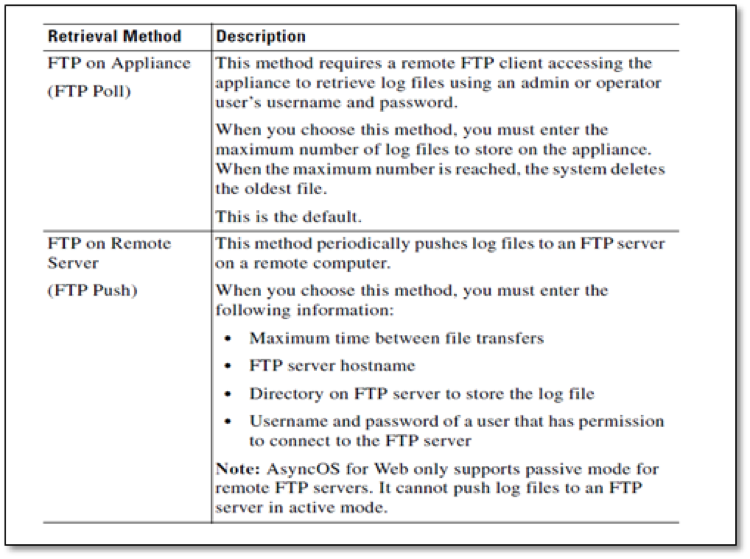
There are four options for log retrieval, as shown. FTP is the default option.