About Skyhigh CASB for Microsoft Teams
IMPORTANT: Going forward, all deployments for Microsoft Teams API Integration must use the Custom OAuth Model. Do not use the Admin Consent Model.
Skyhigh CASB for Microsoft Teams allows Security Operations Center (SOC) Admins to monitor user activity in Teams, enforce DLP policies to make sure that sensitive data violating regulatory and internal compliance policies are not posted in the form of messages or files, and review threats detected by the Skyhigh CASB User and Entity Behavior Analytics (UEBA) and machine learning algorithms.
NOTES:
- Make sure to enable Metered APIs, a prerequisite for completing Microsoft Teams deployment. For instructions on enabling, see Microsoft's guidelines.
- Skyhigh Security now supports Microsoft 365 Copilot users by securing their data on Microsoft Teams. For details on Copilot, see Secure Microsoft 365 Copilot via Skyhigh CASB.
For information about how to enable Microsoft Teams in Skyhigh CASB, see Custom oAuth Application for Office 365 and Azure API Integration.
Using DLP policies, you can extend Skyhigh CASB protection to Teams in several ways:
- Enforce DLP policies in all Teams channels (including the Chat application)
- Monitor messages posted in Teams channels and 1:1/1:many chat conversations (including messages to and from guest users) to make sure confidential data is not shared with unauthorized external parties.
- Monitor files uploaded in Teams to enforce DLP policies.
- Allow/Block access based on managed or unmanaged devices, trusted locations, and more.
- Monitor several types of user and administrative activities performed in Teams to identify anomalous behavior by using machine learning.
- Make sure that only guest users from authorized domains are joining Teams
- Make sure guest users only join specific Teams that allow guest user communication from authorized domains.
- Perform a historical data scan to identify sensitive messages present in 1:1 and 1:many chat conversations (On-Demand Scan)
- Make sure that sensitive data is not shared by internal users with guest users in a Teams meeting chat or group chat.
Microsoft License Requirements
Any one of the following licenses is required:
- Microsoft 365 E5/A5/G5
- Microsoft 365 E5/A5/F5/G5 Compliance [add-on]
- Microsoft 365 E5/A5/F5/G5 Information Protection and Governance [add-on]
- Microsoft 365 F5 Security & Compliance [add-on]
These licensing changes were announced by Microsoft last year where only customers with specific licenses would have access to Microsoft Graph APIs for DLP. Plus, metering charges will be applied to customers based on API usage.
IMPORTANT: E3 is not a valid license for Teams service DLP.
Also please make sure to follow this document from Microsoft to enable the "Metered APIs", which is prerequisite.
Supported DLP Policy Rule Types
- Content/Metadata-only Policies. File Name, File Type, File Path, File Size, Classification - Supported with Skyhigh Security Classification, Data Identifier, Keyword, Regular Expression, Structured Data Fingerprint, and Unstructured Data Fingerprint
- Content-aware-Collaboration Policies. 'Collaboration - Folder/File Collaboration' rule with Data Identifier, Keyword, and Regular Expression rules. Content-aware collaboration is supported only for sensitive messages posted in channels with guest members. Guest members are identified according to the emails, and domains specified in 'to' field of Folder/File Collaboration rule.
NOTE: Content-aware collaboration (as described above) is supported for messages posted in Teams channels and also for messages posted in 1:1 or 1: many user chats in the Chat app. This, in addition to the content-aware collaboration of files uploaded in Teams are supported. Also note that Chat logs are stored in OneDrive, not SharePoint.
Supported External User Communication in Teams
In Microsoft Teams, there are two types of users that are not considered internal:
- Guest users. Guest users are external users added as guests in an organization's Azure AD (Office 365). This type of guest user can be added to any team; other users can initiate a chat conversation involving this guest user.
- By default in new Teams tenants, Guest Access is disabled and must be enabled.
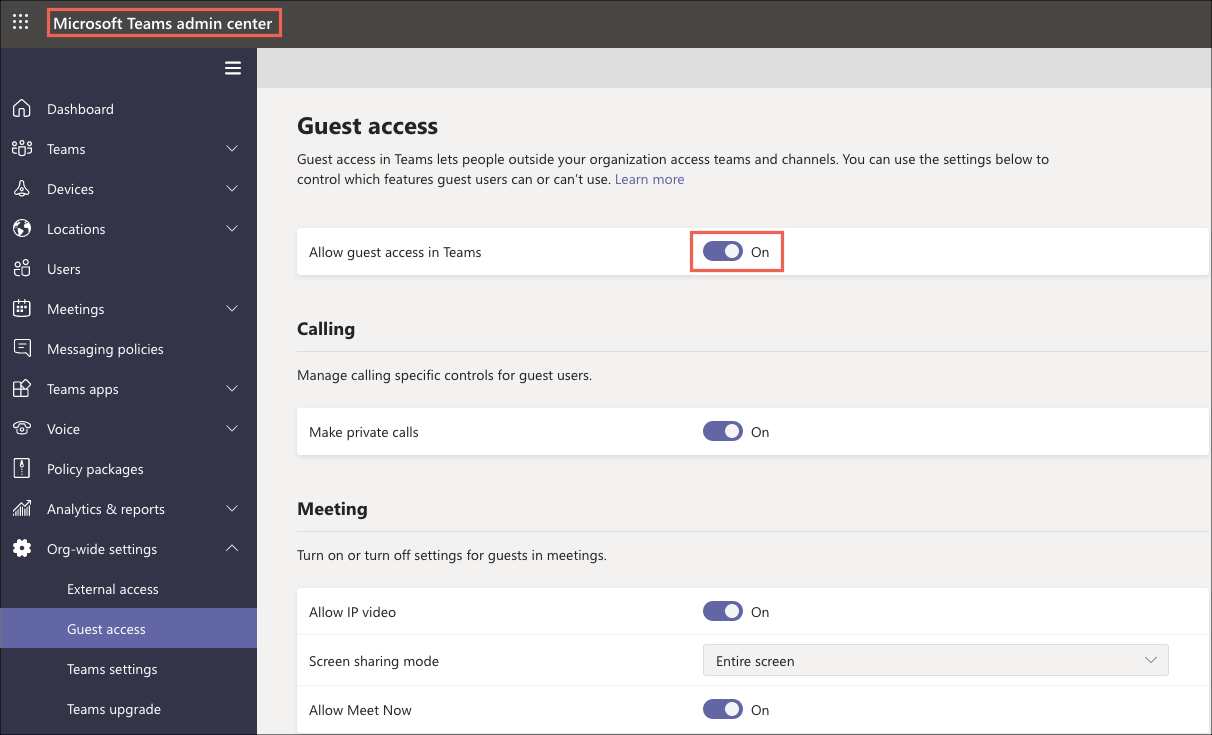
- By default in new Teams tenants, Guest Access is disabled and must be enabled.
-
External users. These users are not added as guests to an organization's Office 365 account, you can learn more here. Skyhigh CASB only has partial support for this use case.
-
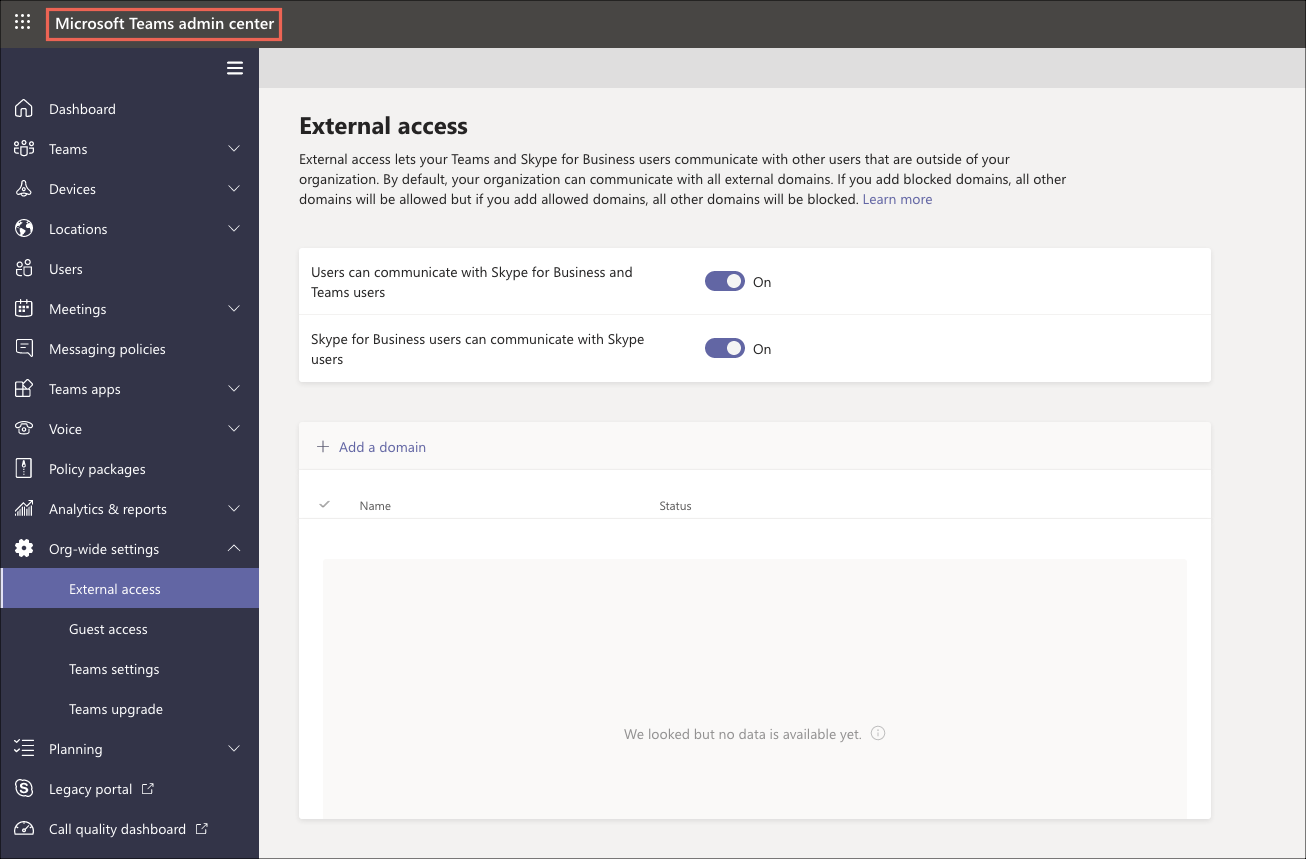
External access lets your Teams and Skype for Business users communicate with other users that are outside of your organization. By default, your organization can communicate with all external domains. If you add blocked domains, all other domains will be allowed but if you add allowed domains, all other domains will be blocked. Learn more
-
|
Channel Type |
Policy Type |
External User Type |
Supported |
|---|---|---|---|
|
Regular channel in a team |
Content/Metadata-only Policies |
Guest |
Yes |
|
Regular channel in a team |
Content-aware-Collaboration Policies |
Guest |
Yes |
|
Regular channel in a team |
Content/Metadata-only Policies |
External |
No |
|
Regular channel in a team |
Content-aware-Collaboration Policies |
External |
No |
|
1:1 or 1:many chats |
Content/Metadata-only Policies |
Guest |
Yes |
|
1:1 or 1:many chats |
Content-aware-Collaboration Policies |
Guest |
Yes |
|
1:1 or 1:many(group) chats |
Content/Metadata-only Policies |
External |
Partial Support* |
|
1:1 or 1:many chats |
Content-aware-Collaboration Policies |
External |
Partial Support* |
* If a chat conversation/thread is initiated by an internal user with any external user, then this conversation can be monitored by Skyhigh CASB for DLP. If the thread is initiated by the external user, Skyhigh CASB doesn't have visibility into the chat messages as Teams APIs do not notify Skyhigh CASB for these messages.
DLP Policy Response Actions
Unless specified, the following Response Actions can be used for both messages and files posted in Teams:
- Send Email Notification
- User Email Notification
- Delete
- Quarantine (supported only for files posted with a message)
- Modify permission to None (to remove guest user)
NOTE: Currently, you cannot customize the tombstone message displayed to users when a message is deleted. This will be supported in a future release.
Reverse Proxy for Microsoft Teams
Skyhigh CASB Reverse Proxy integration for Microsoft Teams supports the following features:
- 1:1 or 1: many (group) chats.
- View, upload, download, and share files in chats. The supported file types are PPT, XLS, XLSX, CSV, PDF, PPTX, TXT, DOC, DOCX, JPEG, GIF, and PNG.
- Upload/download files to and from OneDrive respectively.
- Calendar, meeting invites, and meeting notes.
On-Demand Scan (Limited Availability Feature)
Skyhigh Security Skyhigh CASB for Microsoft Teams allows Security Operations Center (SOC) Admins to create On-Demand Scan to scan the existing messages in 1:1 and 1:many chat conversations in Teams.
Apart from standard On-Demand Scan filters to scan by date range and based on users, it is also possible to scan 1:1 or 1:many chats with guest or external users.
NOTE: On-Demand Scan for Microsoft Teams is for limited availability. To enable this feature, you need to contact Skyhigh Security Support.
