Configure Certificate Checks for Cloud Access Policy
You can configure Skyhigh CASB to perform a certificate check on devices that are connecting to Sanctioned IT cloud services.
Prerequisites
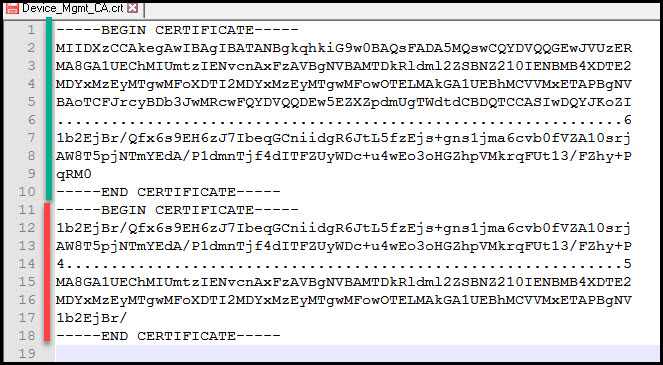
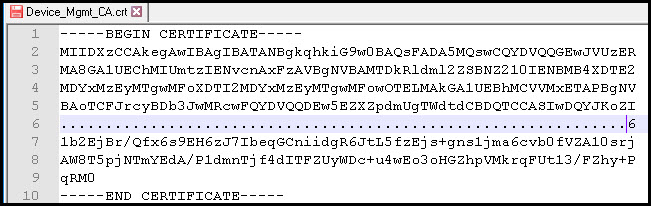
- Provide a copy of your Root CA certificate in base64 format, which is used to sign client certificates. A certificate file in the right format looks like this:
- Microsoft Office 365 clients might require you to enable Active Directory Authentication Library (ADAL) on the device for certificate checks to work correctly.
Configuration
- Log in to Skyhigh CASB.
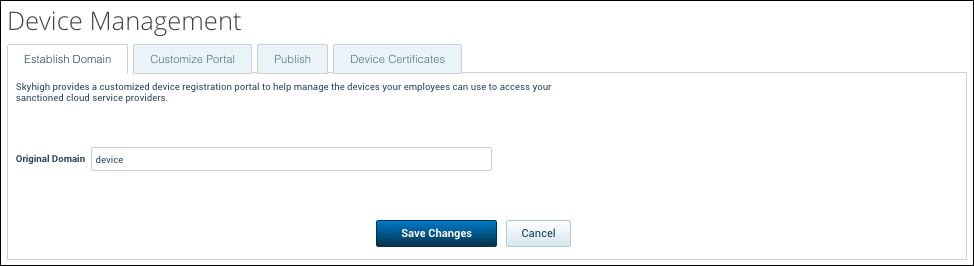
- Navigate to Policy > Access Control > Device Management.
- In the Establish Domain tab, for Original Domain enter devmgmt.
- Click Save Changes.
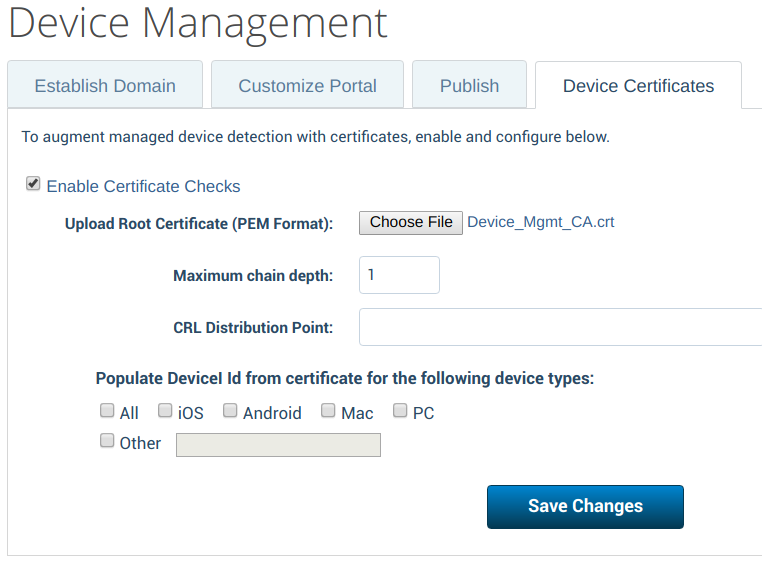
- Select the Device Certificates tab, and set the following:
- Select the Enable Certificate Checks checkbox.
- For Upload Root Certificate (PEM Format), select the Root CA certificate file (base64 encoded).
- For Maximum chain depth: This defines the hierarchy of the certificate trust. If your device certificates are issued directly by the Root CA, enter 1. If there is an Intermediate CA between the Root CA and the device certificate, enter 2.
- Keep the default for all other settings, unless you integrate with an MDM solution.
- Click Save Changes.
Using Multiple Trusted Root CAs
It is possible to import multiple Root CAs as trusted CAs by concatenating the certificates into one single file before uploading it to Skyhigh CASB.
To do so, open both base64-encoded certificate files with a text editor, and copy and paste the text together.
The following is an example of how a compatible file looks with two Root AC certificates combined. The green line displays the "Certificate 1" section, and the red line displays the "Certificate 2" section.