Skyhigh CASB Architecture
Architects considering a CASB need to be aware that there are three primary methods in which CASB services are applied to corporately-sanctioned cloud providers (see Figure 1, CASB Architecture):
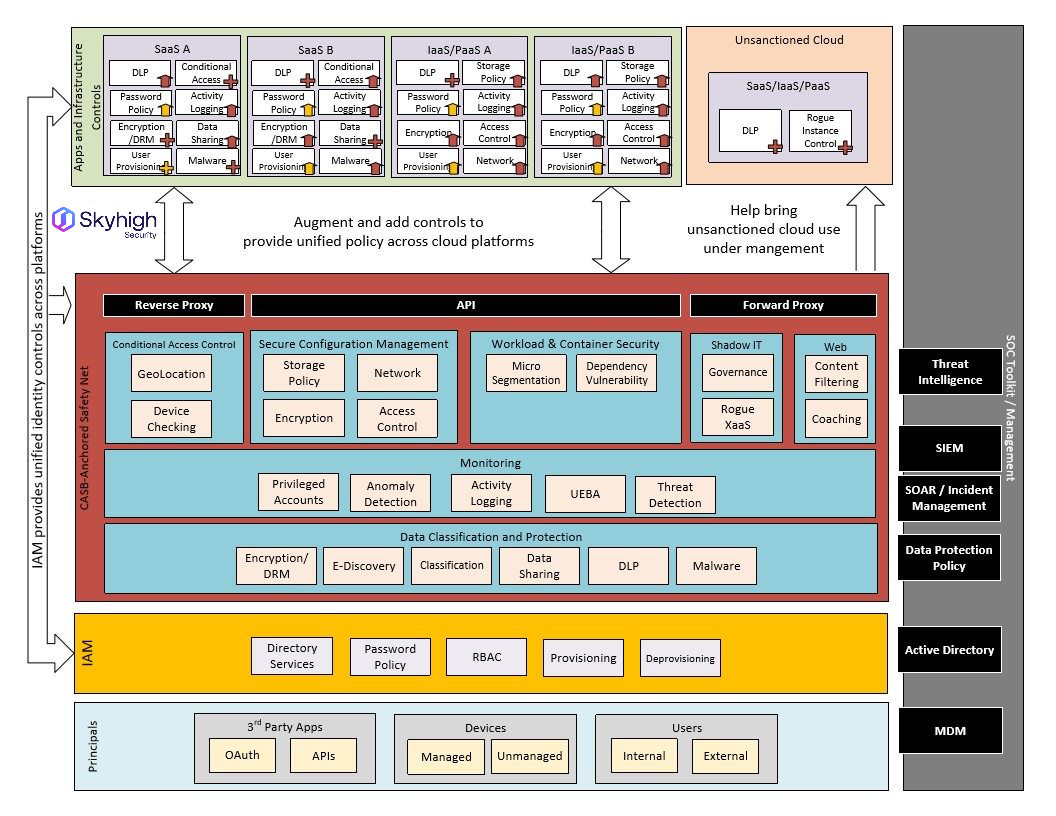
Figure 1 - CASB Architecture
API
Security services applied through APIs have the advantage of having a frictionless, 100% native application experience for the users. In this deployment mode, the CASB relies on a streaming activity feeds from the CSP and enforces security on a near real-time basis by making API calls back into the service.
Reverse Proxy
Leveraging a reverse proxy has the advantage of applying security in-line without the need for agents, SSL decryption, and other complexity that can be associated with forward proxies. Instead, reverse proxy is inserted into the traffic flow by modifying the SAML endpoint in the cloud application’s entry in the customer’s identity provider. When traffic is directed through the reverse proxy, it can perform functions such as conditional access control, DLP, and activity monitoring.
Forward Proxy (Skyhigh SWGS)
Forward proxies are a classic mainstay of web security that are positioned well to protect the "on-ramp" to the cloud. In the context of cloud security, forward proxies continue to play a major role in detecting, preventing, and coaching users away from hazardous cloud use and towards corporate sanctioned cloud solutions. Skyhigh Security offers Skyhigh Web Security Gateway Service as either a SaaS or on-premises solution. As a SaaS solution, Skyhigh Web Security Gateway Service can be configured as either a complete solution or one that complements existing proxy or firewall infrastructure by tunneling only selected cloud traffic. While it is commonplace and workable to have a different vendor provide for the API and Reverse Proxy components of CASB, there are benefits to a single-vendor solution including a consolidated dashboard, DLP policies, and investigation workflows.
