HTTPS Connection Options — Set Up Secure Connections and Configure Exceptions
You can configure the HTTPS scanning process on Secure Web Gateway to allow exceptions. For this purpose, you fill web objects you want to exempt from HTTPS scanning in lists for use by suitable rules.
- On the user interface for Secure Web Gateway, select Policy > Web Policy > Policy.
-
On the policy tree in the navigation panel, expand HTTPS Scanning and select HTTPS Connection Options.
The selected rule set appears in the configuration area on the right. -
Configure when this rule set should apply.
-
Under Criteria, leave the default All traffic, as you want the rules in this rule set to apply to all types of traffic.
- Next to Applies to, leave the default Request, as you want the rules in this rule set to be processed in the request cycle of web filtering on Secure Web Gateway.

-
-
Click the settings icon to configure settings for this rule set in a panel that is inserted on the right. The settings that are currently in use are shown as selected on the panel.
These settings allow you to configure for secure connections. For example, you can configure the use of a particular root certificate, the SSL protocol version, or how to perform a handshake. -
To allow requests for accessing some websites to skip HTTPS scanning, configure lists for the rules that are preset here for this purpose. They are shown under Preset Rules.
Click the three dots at the end of the line with a rule and work with the options for list handling that are provided.
HTTPS scanning is skipped for requests to acces the items that you enter in the lists. There are rules with lists for entering:-
Domains and hosts
-
WebEx servers
-
Citrix servers
-
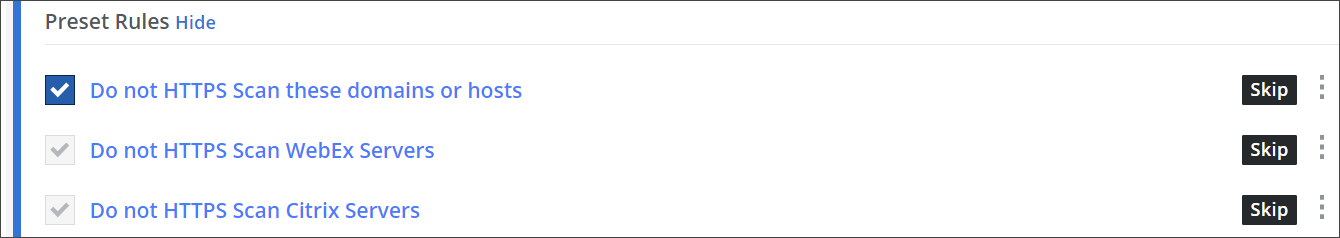
Use its checkbox to enable or disable a rule. To enable or disable the complete rule set, use the On/Off toggles at the end of the line with the rule set name.
The HTTPS scanning process now follows what you have configured for the rules that allow web objects to bypass the scanning.
