Global Block Lists — Block Access to Web Objects Globally
You can block access to web objects, for example, domains or IP addresses, globally. For this purpose, you fill these objects in lists for use by suitable web policy rules.
When a request for web access is received on Secure Web Gateway where one of these objects is involved, for example, a request to access a particular domain, it is blocked. It is not forwarded to its destination, so the user who sent the request cannot access the web object.
- On the user interface for Secure Web Gateway, select Policy > Web Policy > Policy.
-
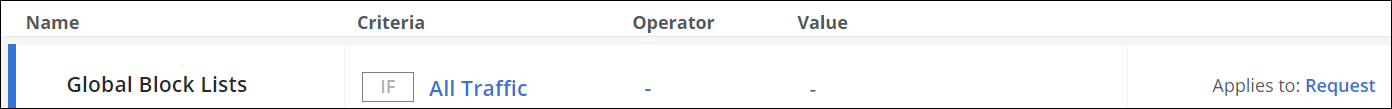
From the policy tree in the navigation panel, select Global Block > Global Block Lists.
The selected rule set appears in the configuration area on the right. -
Configure when this rule set should apply.
-
Under Criteria, leave the default All Traffic, as you want the rules in this rule set to apply to all web traffic.
- Next to Applies to, leave the default Request, as you want the rules in this rule set to be processed in the request cycle of web filtering on Secure Web Gateway.
-
- Configure the rules that are preset in this rule set as needed.
These rules are shown under Preset Rules. For example, there is a rule named Domains Blocklist, which blocks access to domains that you enter in a list.

a. Enable or disable any of these rules. Use the toggle checkbox at the beginning of the row for a rule to do this.
There are preset rules that block web objects of the following types:
-
Domains
-
Connected IP addresses
- Client IP addresses
-
Destination IP addresses
-
User groups
-
User names
- Processes
b. Enter domains and other web objects in lists for use by these rules. Click the three dots at the end of the row
for a rule and work with the options for list handling that are provided.
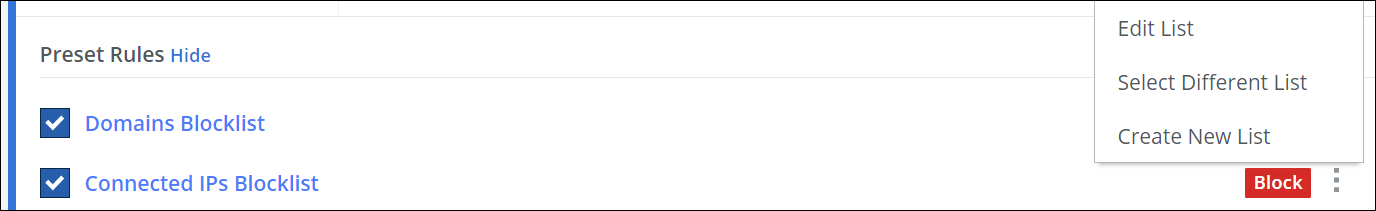
You can also create rules of your own and add them to this rule set. Click the three dots at the end of the top row and work with the options of the drop-down menu to create a new rule.
This menu also includes an option for reviewing and working with the underlying code for a rule set.
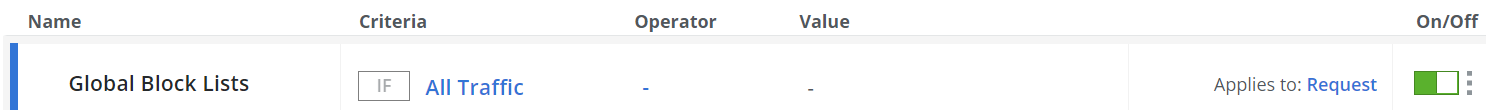
To enable or disable the complete rule set, use the On/Off toggles.
The filtering process now follows what you have configured for the rules that block web objects globally.
