Access the Web Policy Code View
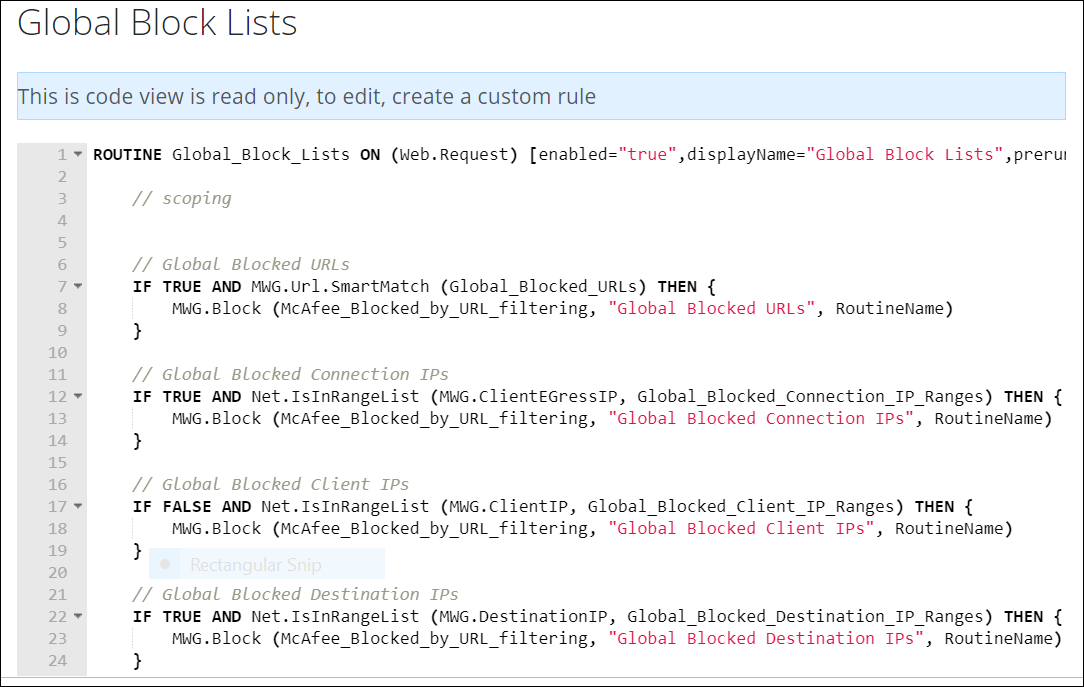
The web policy code view shows the code that underlies the rules and rule sets of your web policy.
WARNING: If you modify the web policy code incorrectly, the web policy functions may fail. Make sure that you understand the code before making changes to it.
To go to the web policy code view, proceed as follows.
-
On the user interface for Secure Web Gateway, select Policy > Web Policy > Policy.
The Web Policy page appears. -
From the navigation panel, select the rule set for which you want to view the code. For example, select Global Block > Global Block Lists.
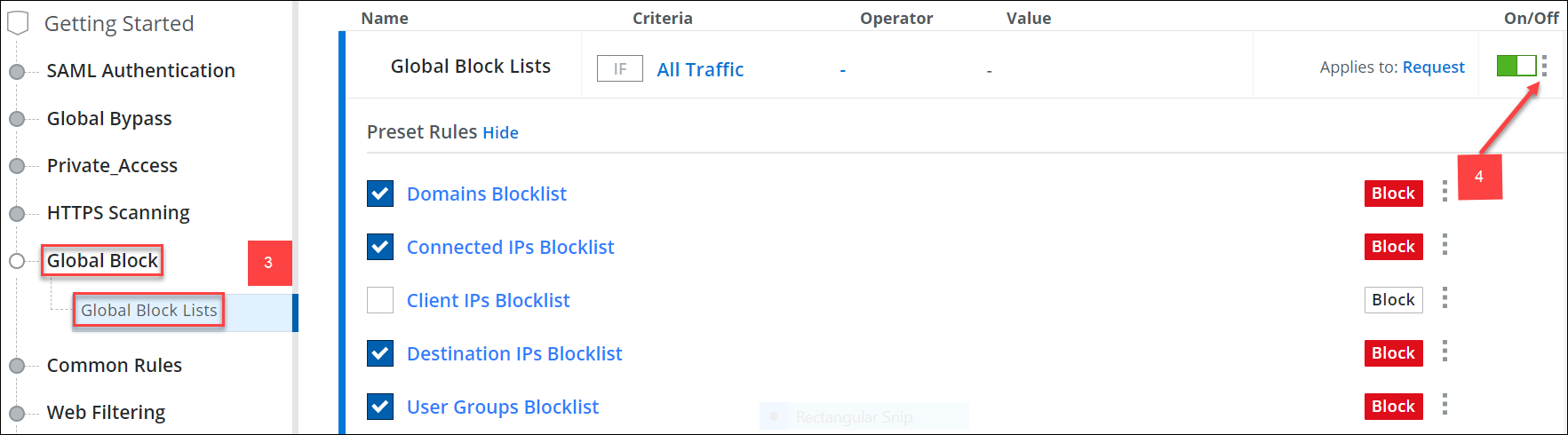
The selected rule set appears together with the rules in the configuration area. -
Click the three dots menu next to the specific rule, then select View Policy Code.
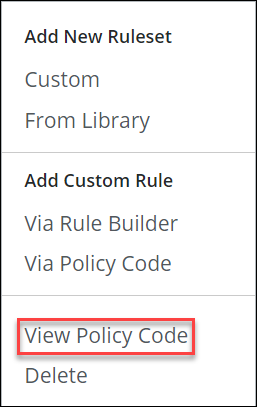
The web policy code for the selected rule set appears.