Configure your Remote Access Card (RMM)
What are Remote Access Cards?
Let’s assume for a moment that you are reading this document and you have never heard of RMM. Remote Access Cards give you basically all the functionality of sitting directly in front of your appliance in your server room, but without all the noise/heat/leaving your desk.
You can reboot -- power on from a true power off -- you can even re-image your appliance if needed. Beyond that, you are able to look at hardware health information and the System Event Log.
Your remote access card operates completely independently from the host system/OS. That means you can reboot your machine, or even power it off entirely, and you can still get access to your appliance. With the remote console, you can even get into your BIOS/RAID controller BIOS if needed, all from the comfort of your workstation outside of the server room and potentially hundreds of miles away from it.
Which SWG appliances have remote access cards?
The following models have remote access cards available:
- 5000A & 5500A - EOL - Configuration for the DRAC was removed from this guide
- 5000B & 5500B - EOL
- 4500C, 5000C, & 5500C - EOL
- 4500D, 5000D, & 5500D
- 4500E, 5000E, & 5500E
How do I set up my remote access card?
The steps are different depending on whether you are using RMM. Both require a unique IP and a separate ethernet connection.
RMM
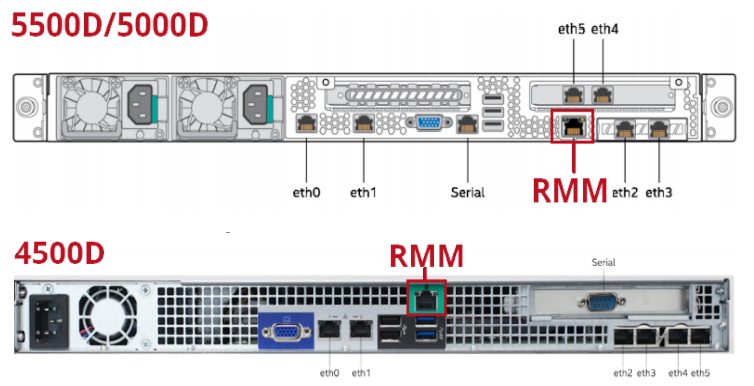
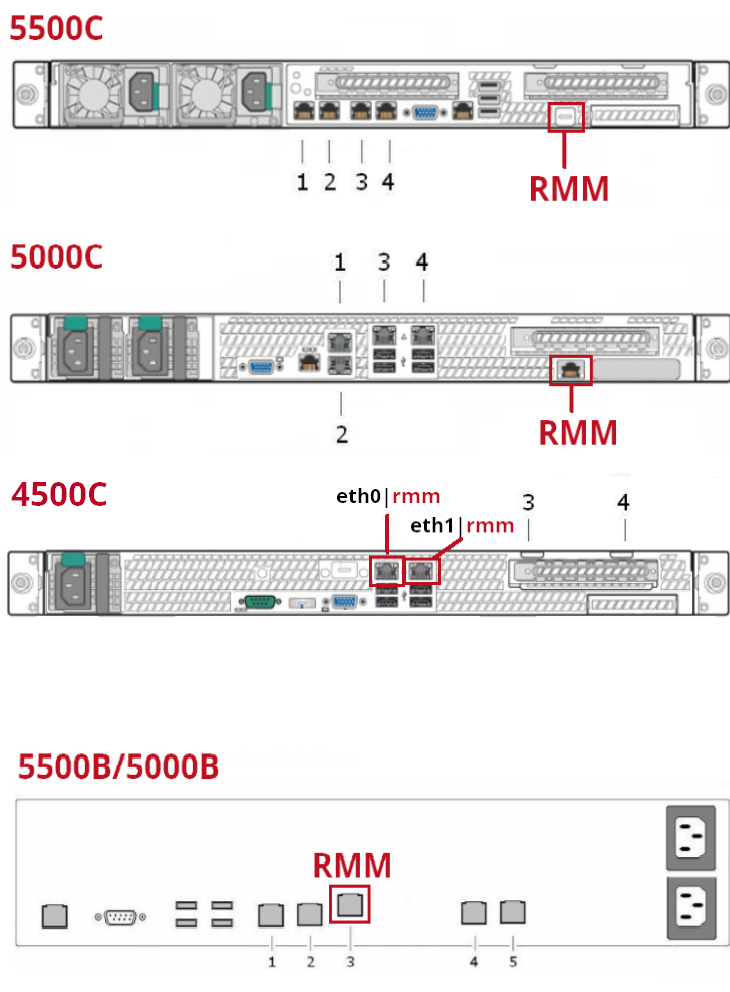
First, connect your RMM to your network, you can find the RMM port on the back of your appliance:
5000E/5500E

4500E

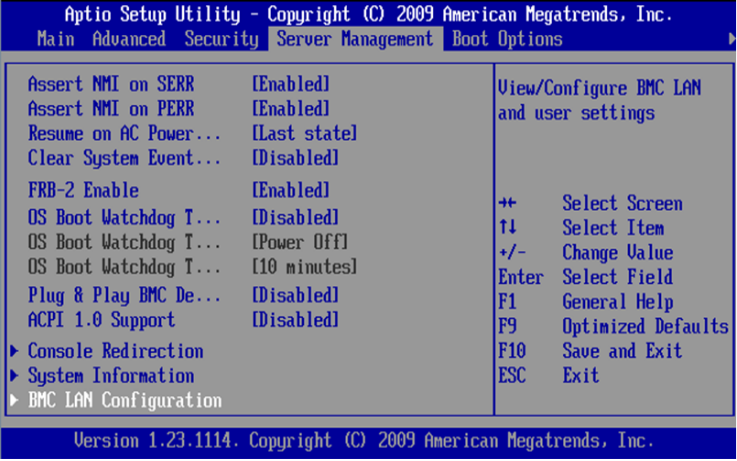
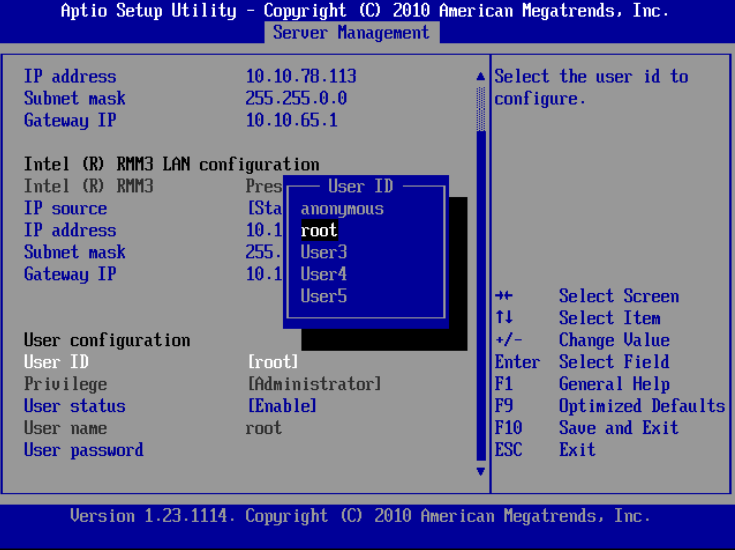
Boot your system into the BIOS (F2 at startup). Navigate to Server Management -> BMC LAN Configuration.
Configure your IP address, subnet mask and Gateway IP for your Intel RMM LAN configuration, as shown here.
NOTE: Do not configure your Baseboard LAN. Enabling both BMC and RMM can cause interface conflicts and lead to problems accessing your RMM.
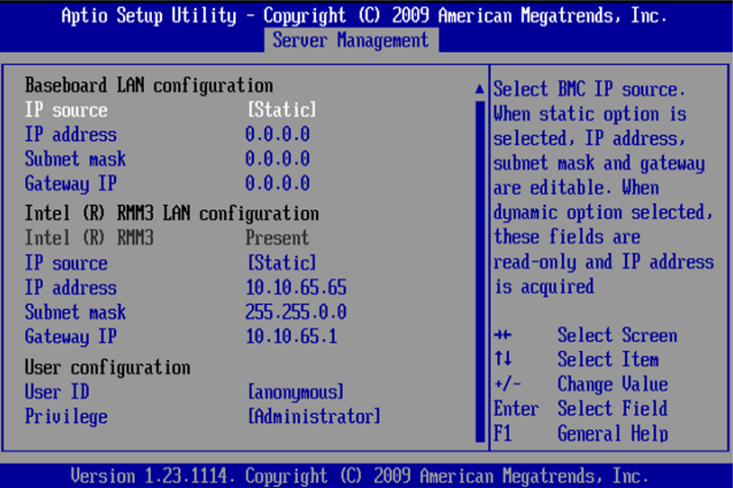
Finally, scroll down to the User configuration section. You can define accounts and set passwords here. For now, just select the root user, and change the password to something you will remember.
Save the changes in the BIOS and exit, then you can allow your box to boot as normal. You should now be able to access your RMM GUI via HTTPS in the browser.
Remote Access Card Usability
Configuring the remote access card ensures you're ready for troubleshooting or re-imaging when necessary. Here are some key RMM functionalities:
RMM
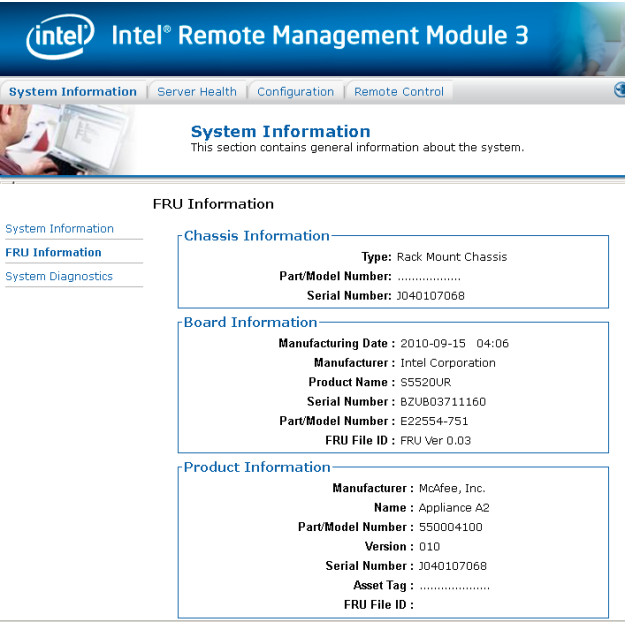
After logging into your RMM - you will be brought to the System Information screen. Unfortunately, there’s not a lot of useful information or links on this tab. To locate your appliance’s serial number, click on the FRU Information on the left-hand side.
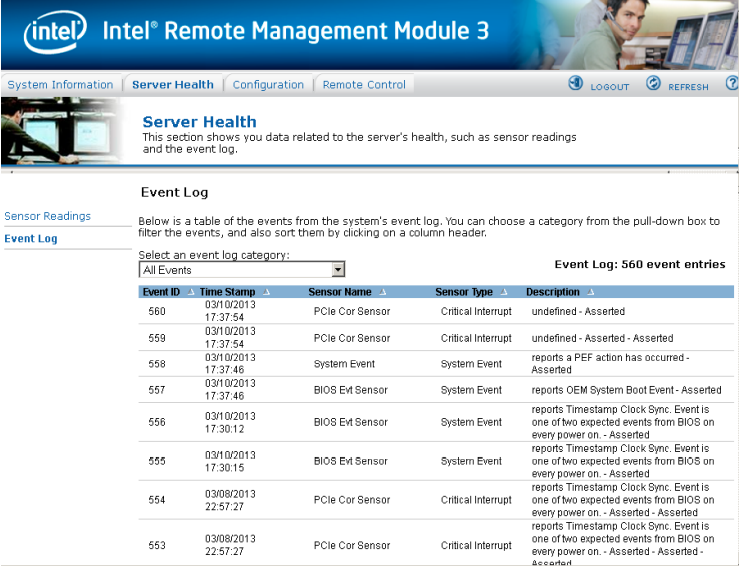
The System Diagnostics section isn't useful for troubleshooting as it produces a password-protected ZIP file that cannot be accessed by either you or SWG Support Engineers. Instead, use the System Event Log under Server Health > Event Log for more effective troubleshooting. This log often provides valuable evidence if you're experiencing hardware issues.
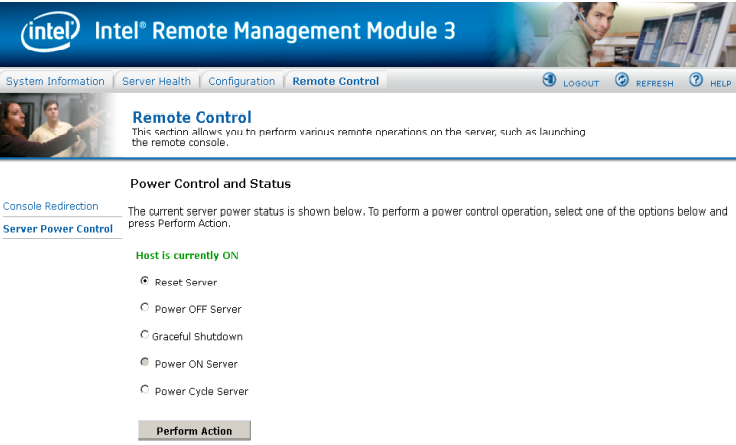
To power on/off or reboot the appliance from your RMM, you can do so under the Remote Control > Server Power Control section.
Most importantly, you can gain access to the remote console under the Remote Control > Console Redirection section of your GUI.

From the JViewer console - you can interact with your appliance as though you were at the physical console - including modifying BIOS/RAID configuration as well as regular console interaction with your SWG and re-imaging.
On the point of re-imaging, if you needed to do so, you can mount an ISO file to the virtual drive under the Device -> Redirect ISO option.
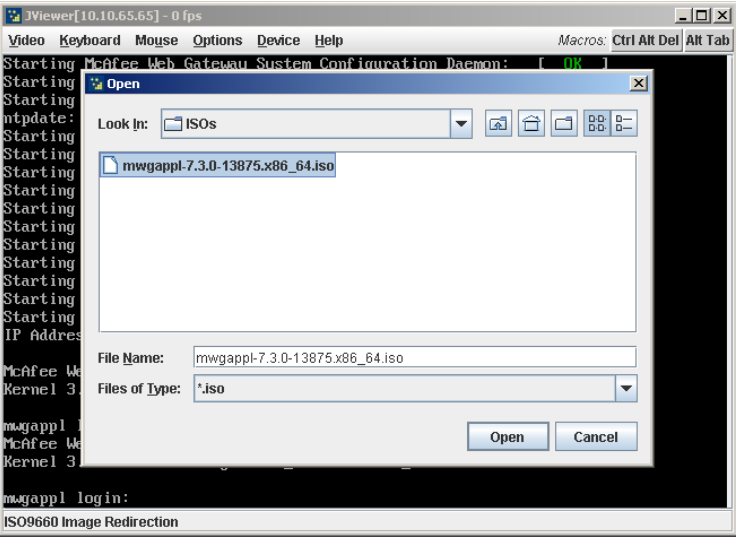
Then, once mounted, you can reboot your machine, and then enter the boot menu by pressing F6 and proceed to re-image your appliance as normal.
Baseboard Management Controller
The Baseboard Management Controller (BMC) provides remote access, monitoring, and management. The system page displays system component details and health information, health events, sensor readings, and storage monitoring if the server is connected to the storage component(s).
BMC Configuration of F models
This section describes how to configure BMC of F models.
WBG 5000F/5500F port assignments:

To configure BMC of F models:
- Log in to the 5000F setup by pressing DEL on the keypad.
- Navigate to the BMC tab and select BMC Network Configuration:

- Select the applicable BMC network and enter the configuration:

- Mark the Update BMC LAN Configuration as Yes and Configuration Address Source as Static, and then assign the IP address, Subnet mask, and Gateway:

- Save the configuration using F4 and reboot the appliance.
For more information about F models, refer Model F Appliances.
BMC Server Diagnosis
The Dashboard and Health Event Log provide all valuable evidence if any hardware issues are experienced:
User Configuration
- Log in to the 5000-F BMC UI using the
<https:// IP> with default username: root and password : < printed on pullout tag>URL. - Select Configuration > Account Services > Users based on the need to add/modify the user with privilege:
Conclusion
I hope this document has highlighted the benefits of configuring your RMM and the significant time savings it can offer. Being able to manage power states, control the console/BIOS/RAID Controller, and perform reimaging from your workstation—rather than being physically present in the server room—makes the initial 5-minute setup time well worth the investment.
