Integrate Skyhigh CASB Inline APIs with Jenkins, GitHub, and Bitbucket
Skyhigh CASB provides a security solution for customers to evaluate the DevOps templates in both offline and inline mode. Using inline mode, you can integrate the repository and CI/CD tools with Skyhigh CASB inline APIs to check for security vulnerabilities present in the DevOps template file. Currently, Skyhigh CASB supports evaluating DevOps templates for AWS and Azure, including Terraform support.
This procedure uses the cloud version of GitHub, Bitbucket, and publicly accessible Jenkins.
Prerequisites
- Create a repository on GitHub. For details, see New Repo on GitHub.
- Create a Bitbucket repository. For details, see Create a repository in Bitbucket.
Install Jenkins
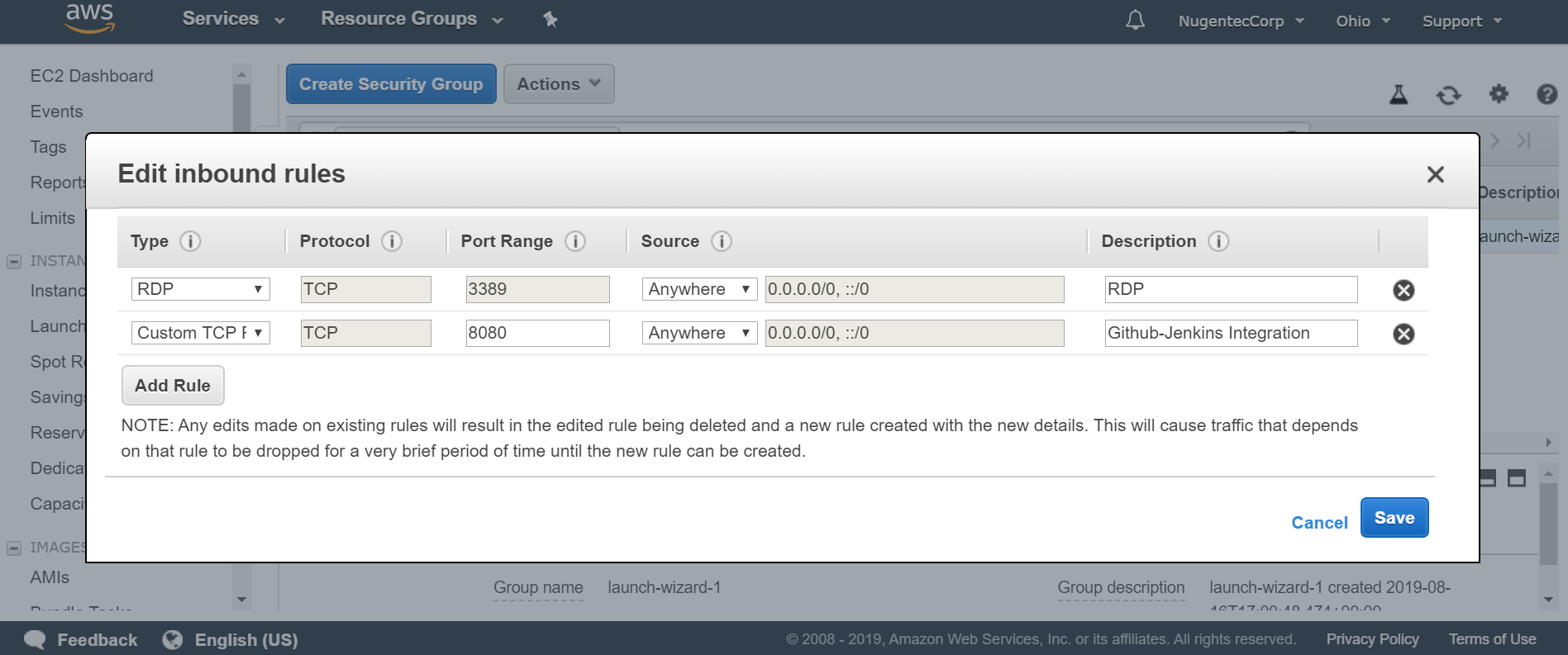
NOTE: Use VMs (AWS and Azure) rather than a physical computer. Open RDP port 3389 and Custom TCP port 8080 in the AWS Security group where the Jenkins EC2 instance resides.
Install Jenkins on Ubuntu
To install Jenkins on Ubuntu:
1. Install Java using the following command:
sudo apt update sudo apt install openjdk-8-jre-headless
2. Install git using the Ubuntu instructions here: https://github.com/git-guides/install-git
3. Install JSON processor library using the below command:
sudo apt-get install jq
4. Install Jenkins using the Jenkins instructions here: Install Jenkins on Ubuntu
Configure Jenkins
Once Jenkins is installed, configure GitHub, Bitbucket, and the Jenkins integration with Skyhigh CASB inline APIs.
- Go to the Jenkins URL (http://<ip-address:port>).
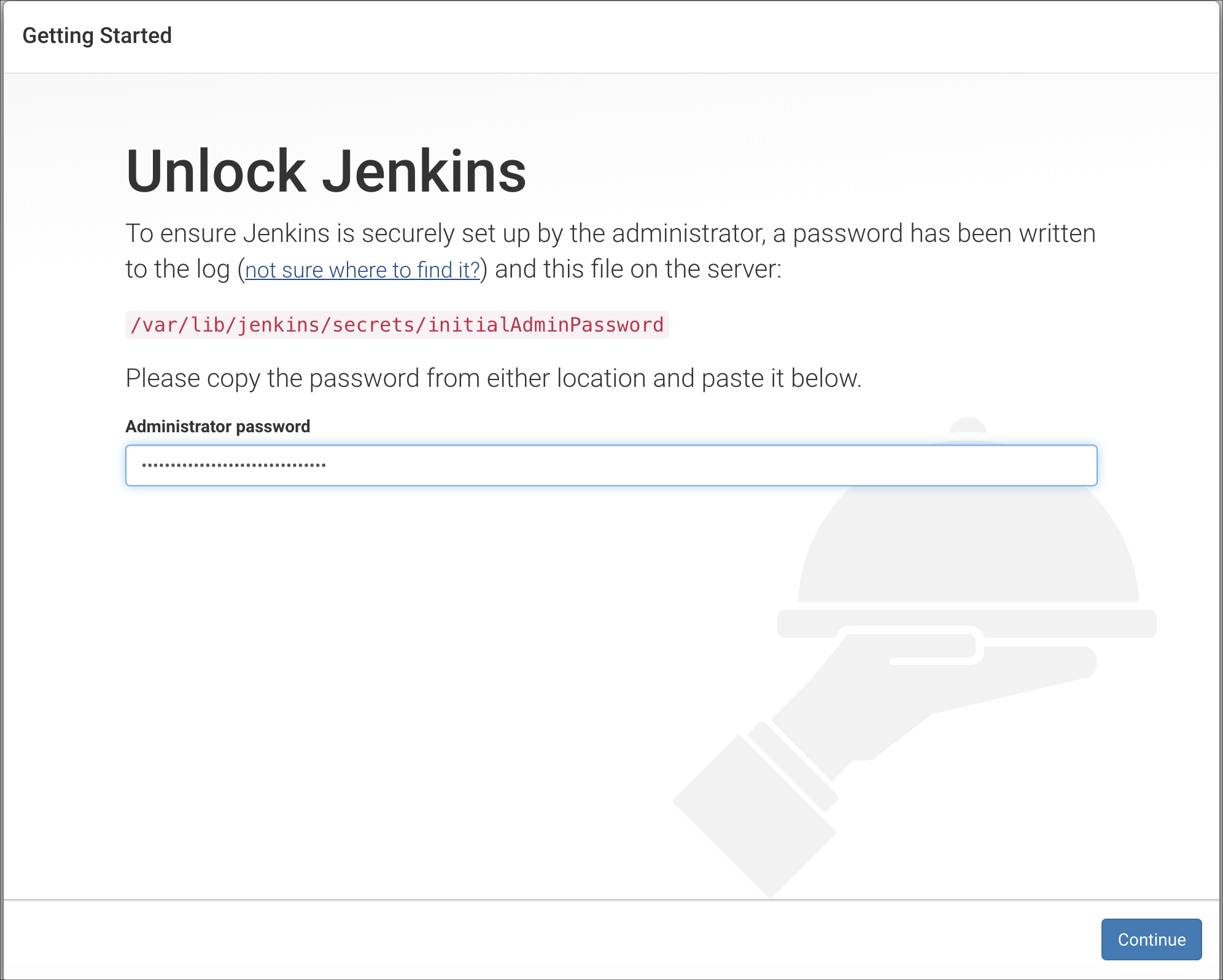
- Follow the instructions on the page to set up Jenkins. Click Continue.
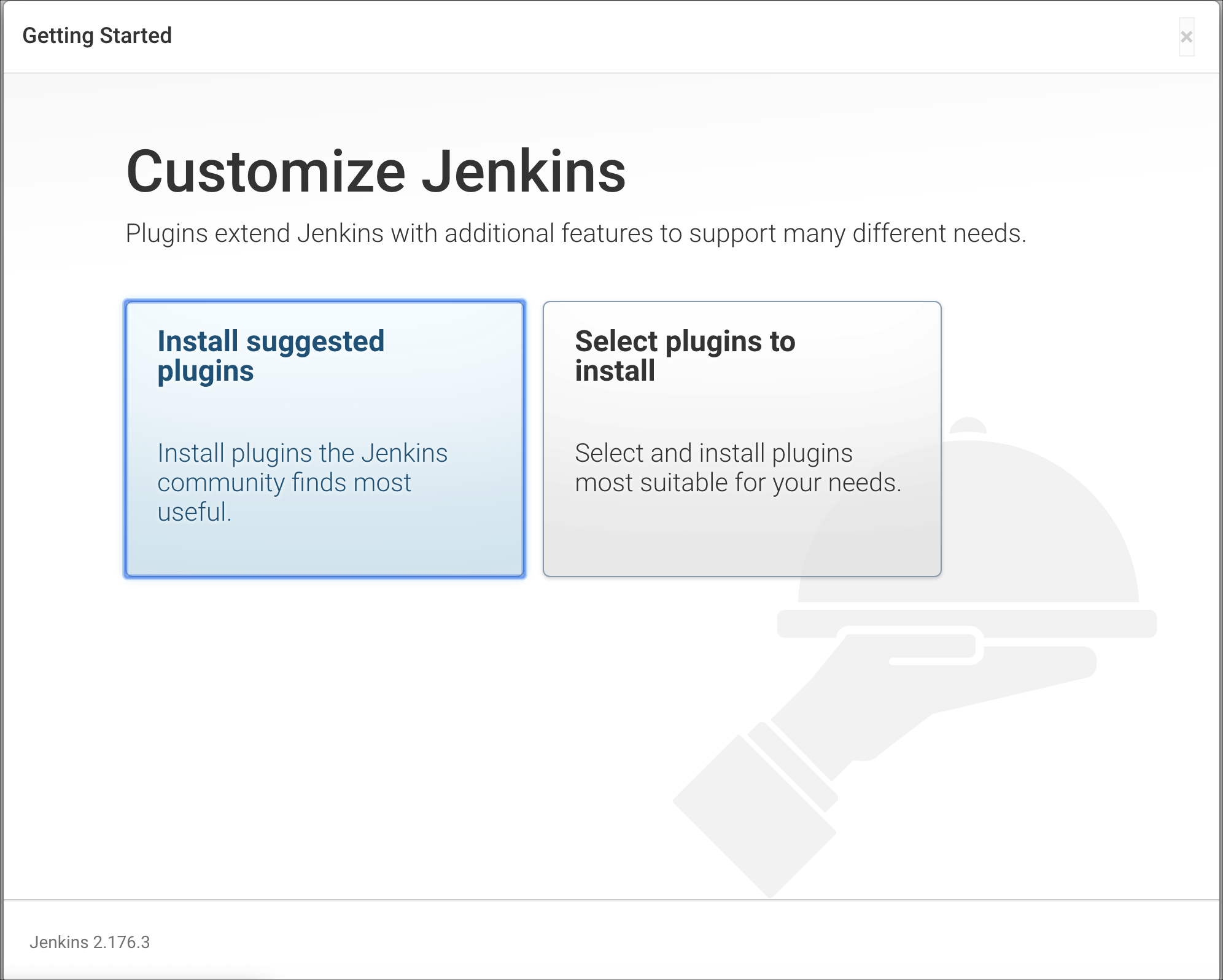
- Click Install Suggested Plugins for Jenkins.
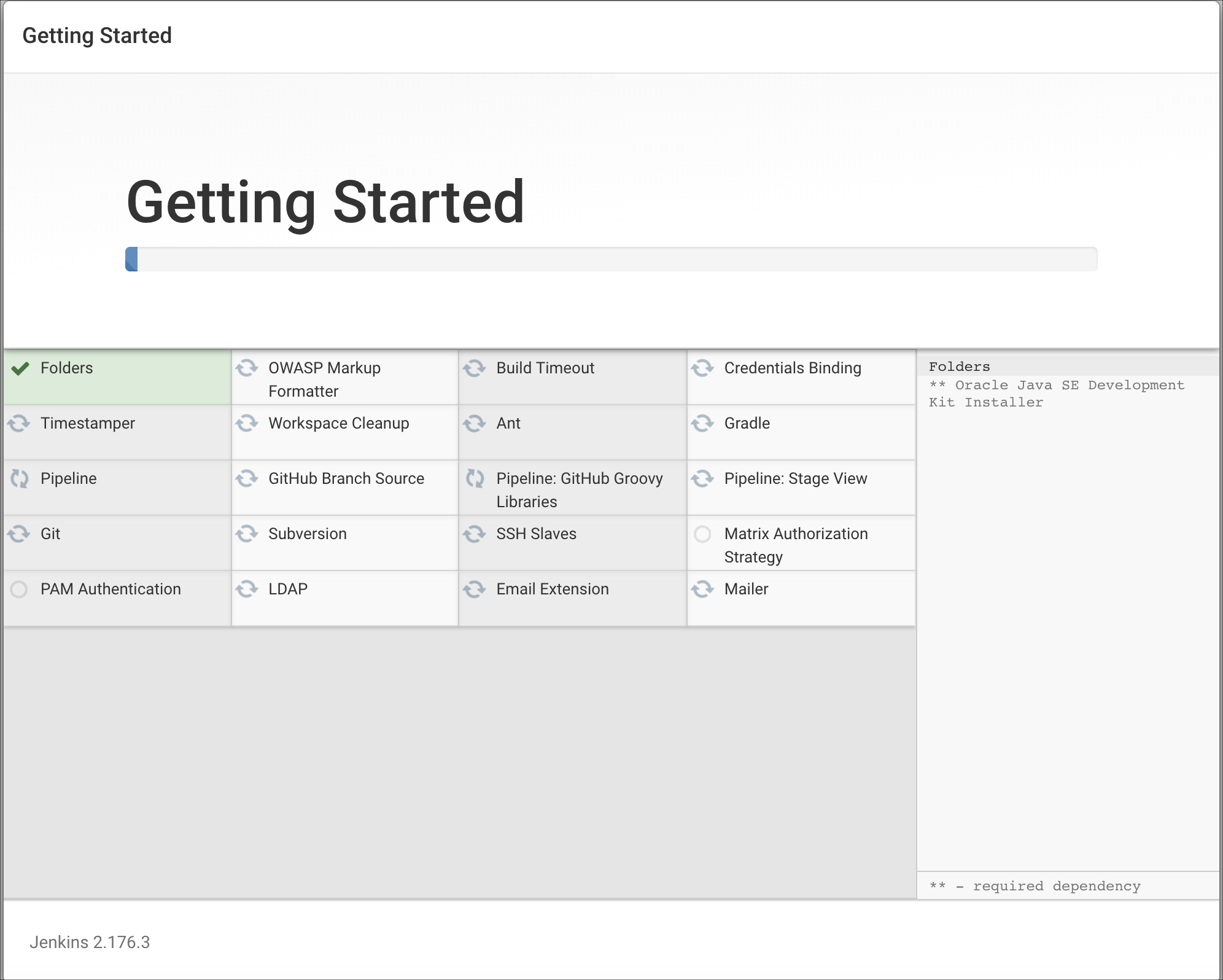
- It installs the suggested plugins as shown.
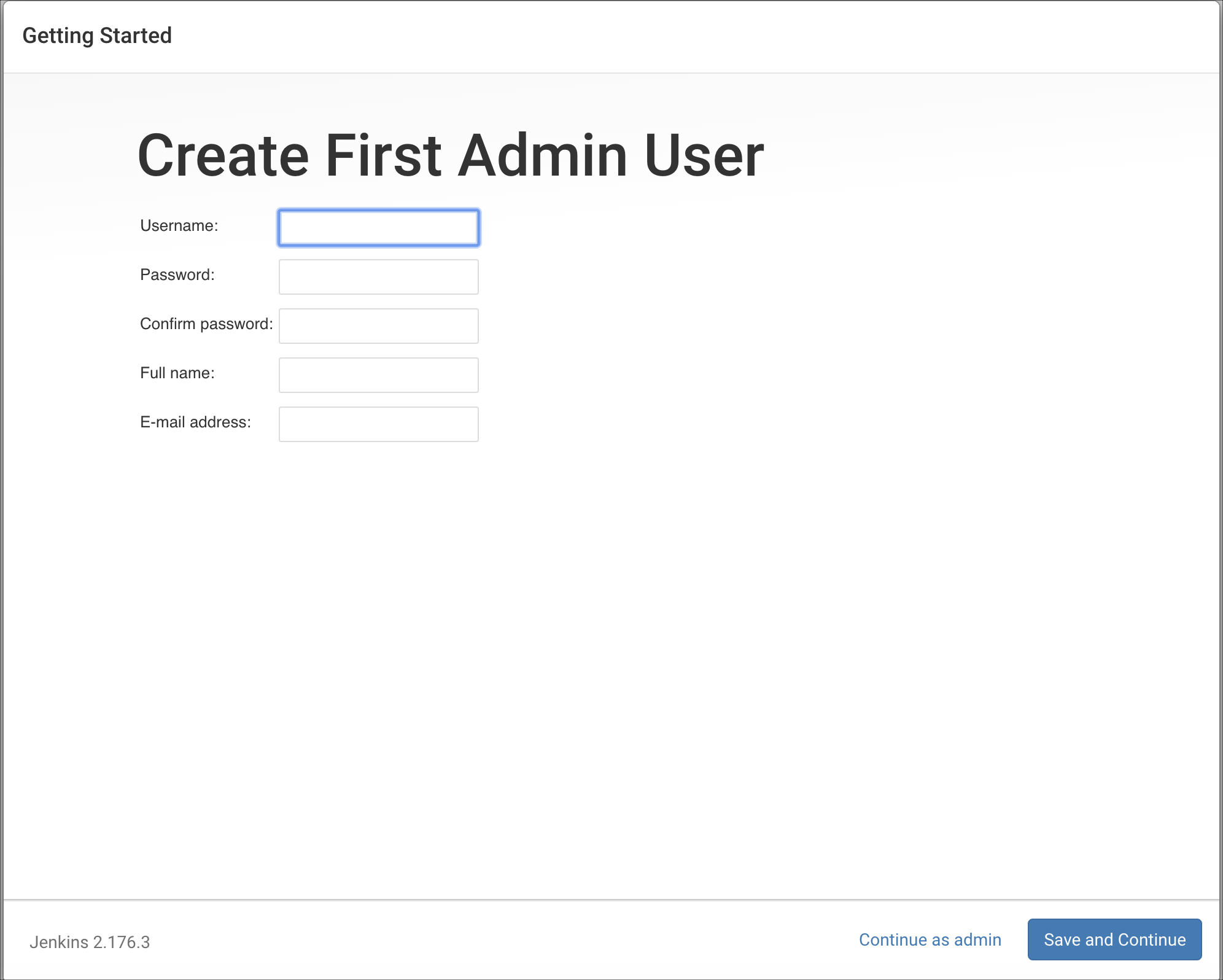
- Create an admin user by filling in the required credentials. Click Save and Continue.
- After Jenkins is configured, you see the screen Jenkins is ready!
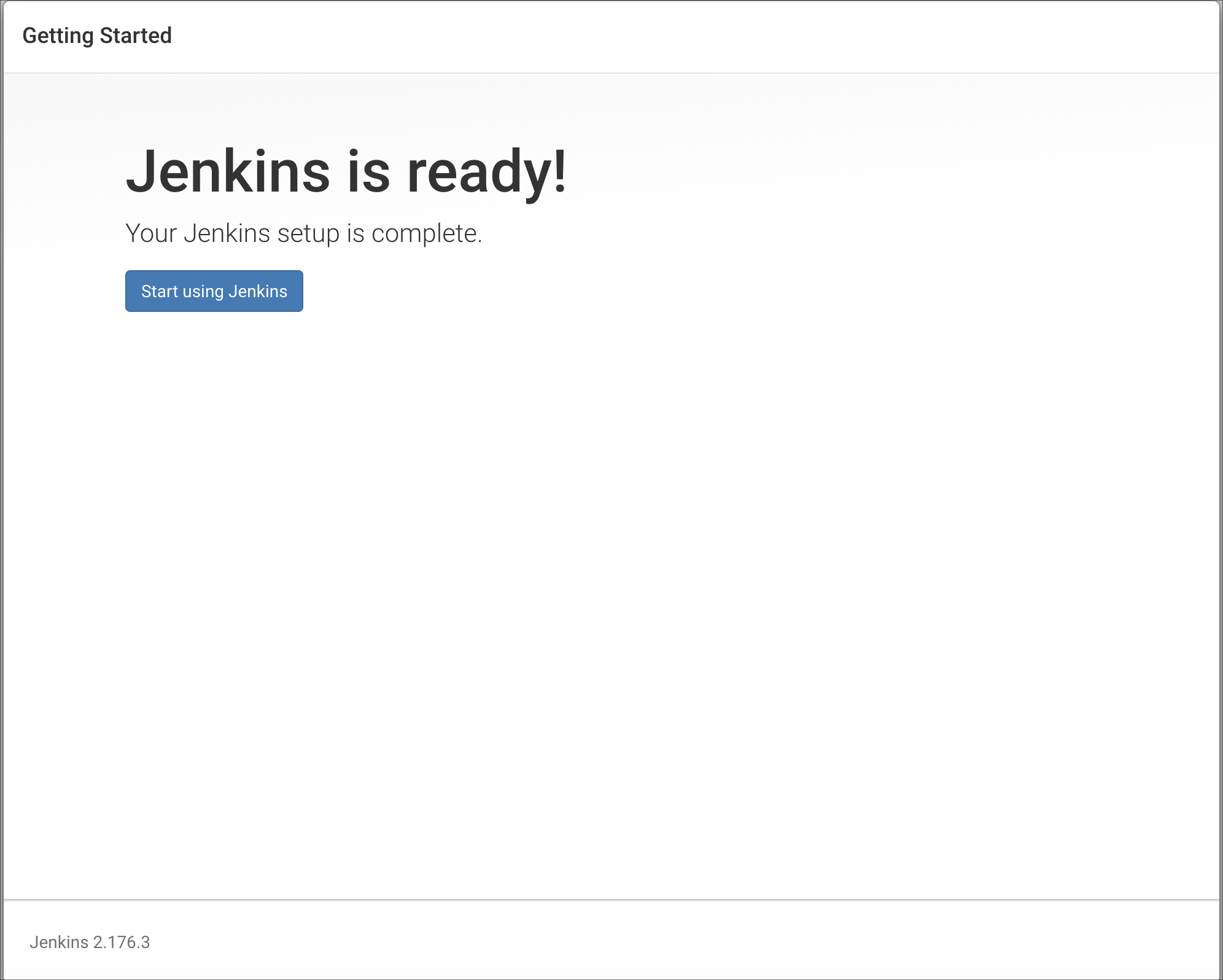
- Click Start using Jenkins.
- The Welcome to Jenkins screen displays.
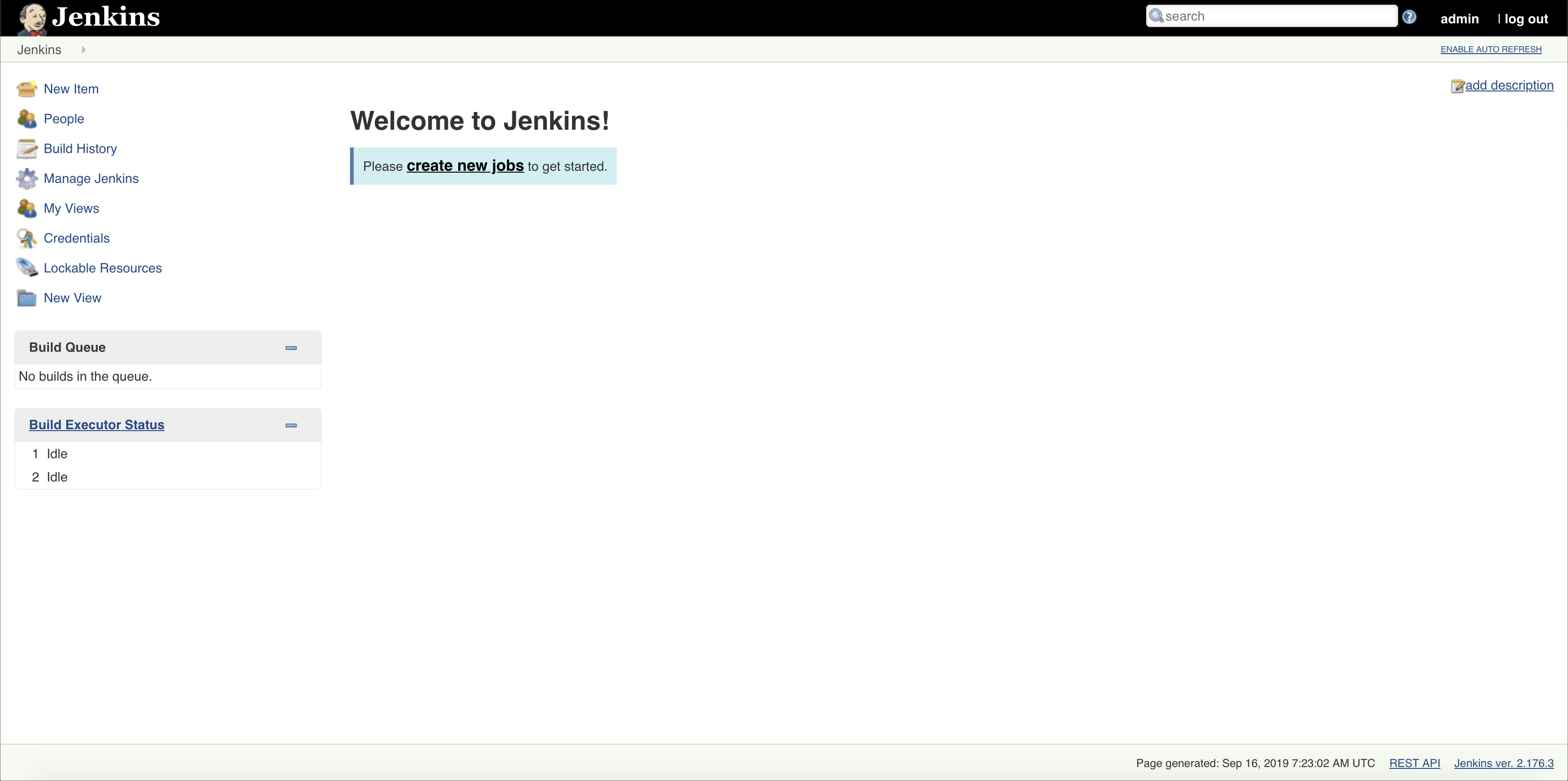
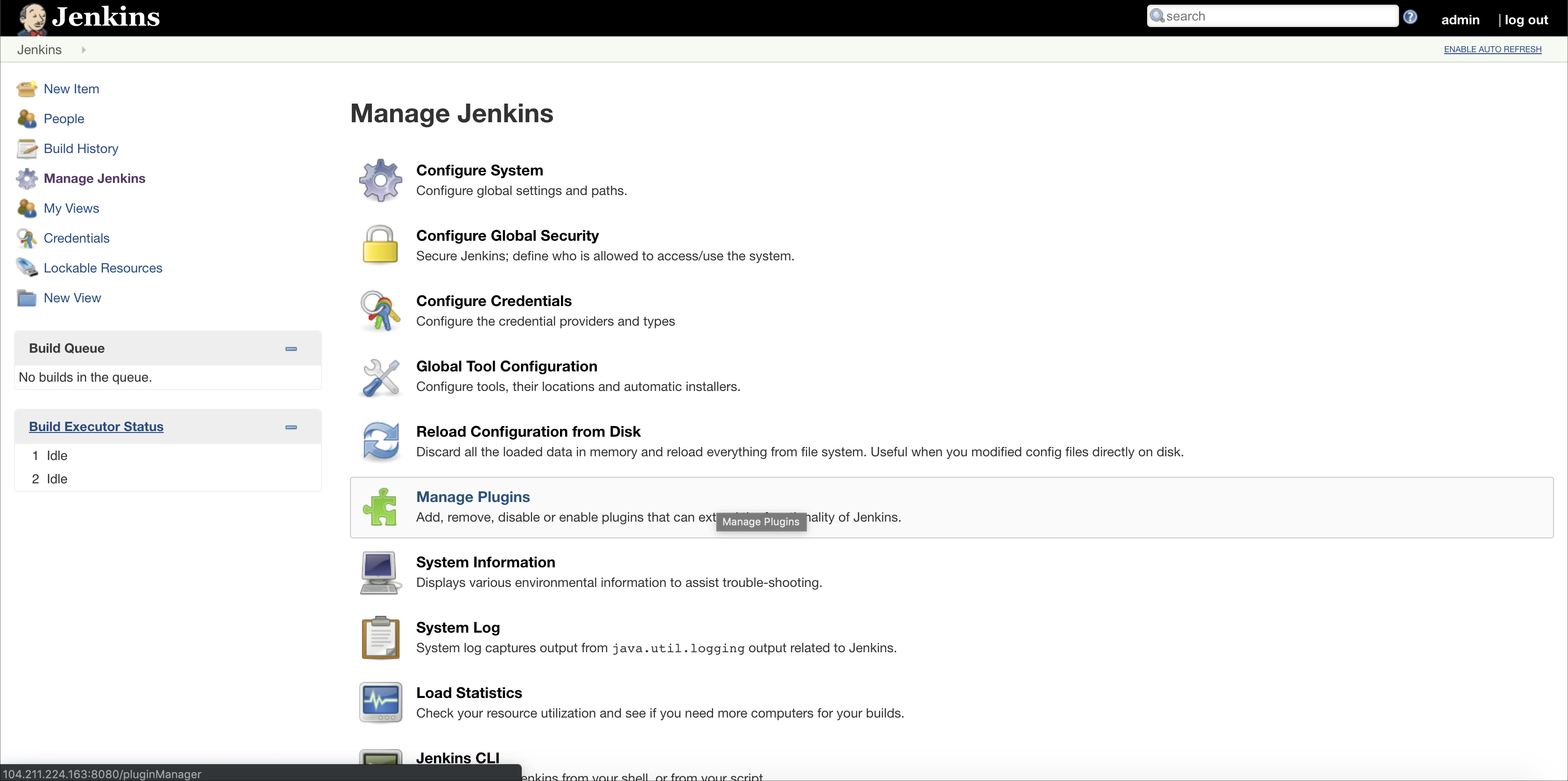
- In the Jenkins homepage, click Manage Jenkins > Manage Plugins.
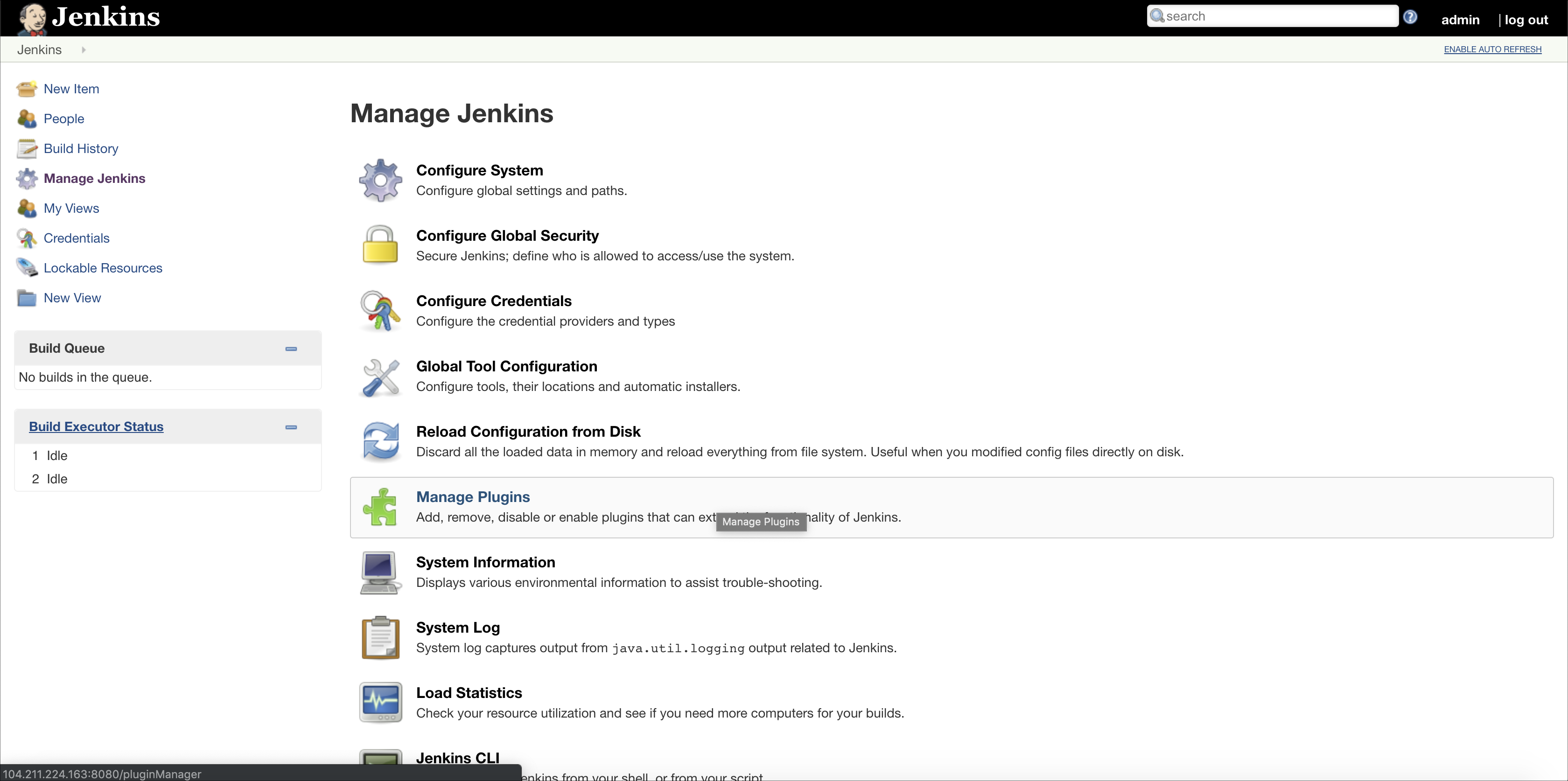
- The Git plugin is installed by default in Jenkins. You don't have to install it.
- To configure GitHub only, skip to step 15.
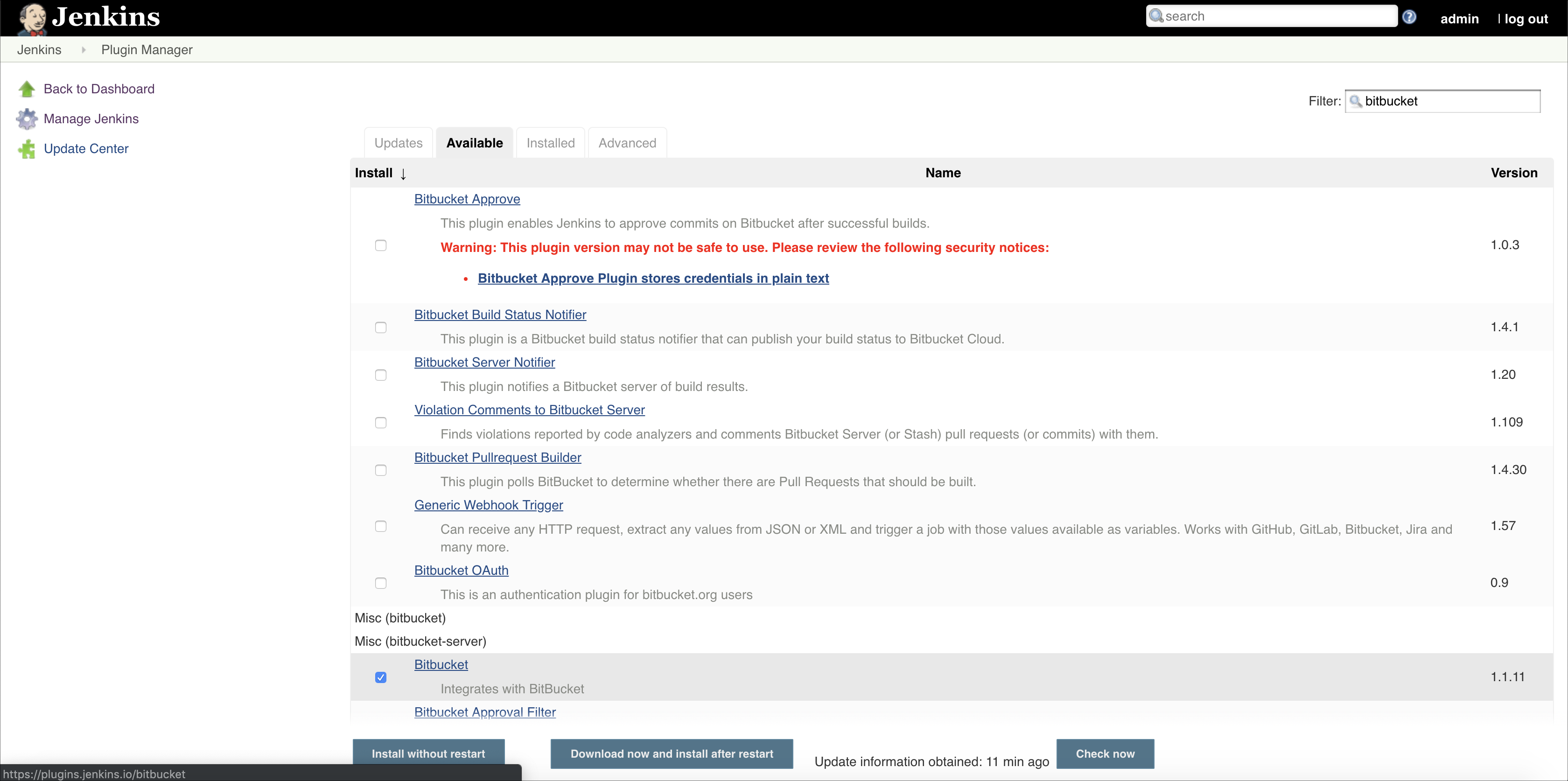
- To integrate BitBucket, in the Manage Plugins page, click the Available tab and search for Bitbucket.
- Select the Bitbucket plugin, and click Download now and install after restart.
- Select the checkbox Restart Jenkins when the installation is complete and no jobs are running.
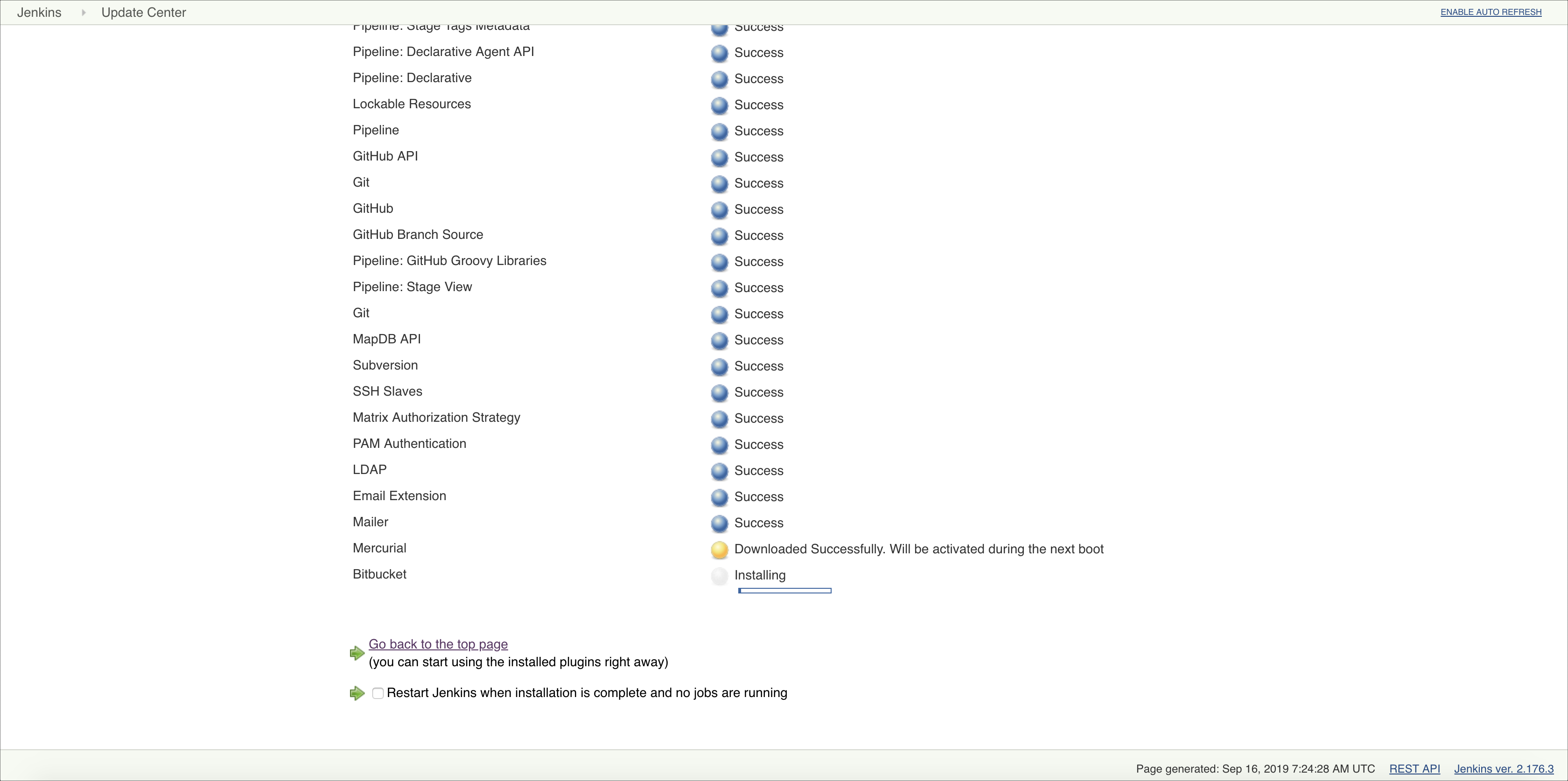
- Jenkins restarts.
- In the Jenkins homepage, click Manage Jenkins. You go to the Manage Jenkins page. Click Manage Plugins.
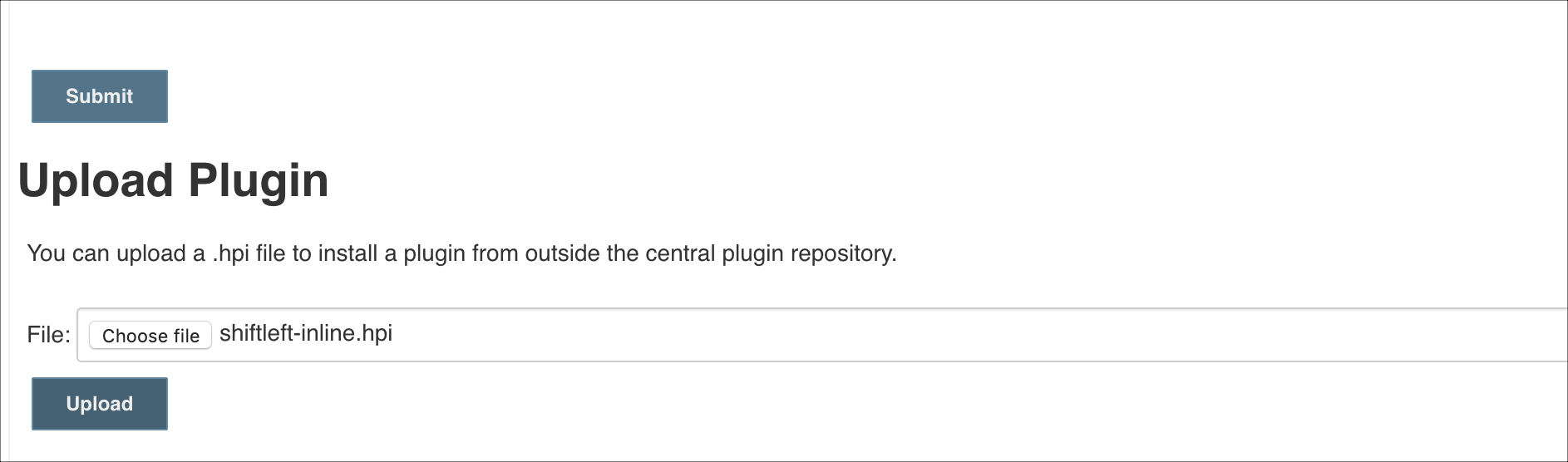
- In the Manage Plugins page, click the Advanced tab. In the Upload Plugins sections, click Choose file, select the file shiftleft-inline-1.0.0.0.hpi, and click Upload.
- Once the installation is complete, select the checkbox Restart Jenkins when installation is complete and no jobs are running. Jenkins restarts and you see the following screen.
- In the Jenkins homepage, click Credentials > System > Global credentials (unrestricted). You go to the Global credentials (unrestricted) page:
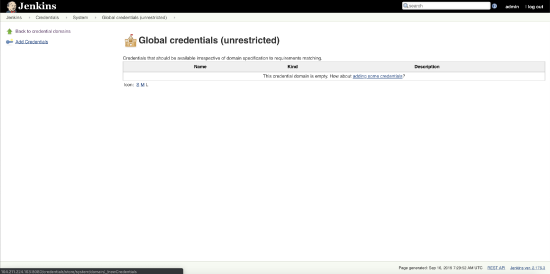
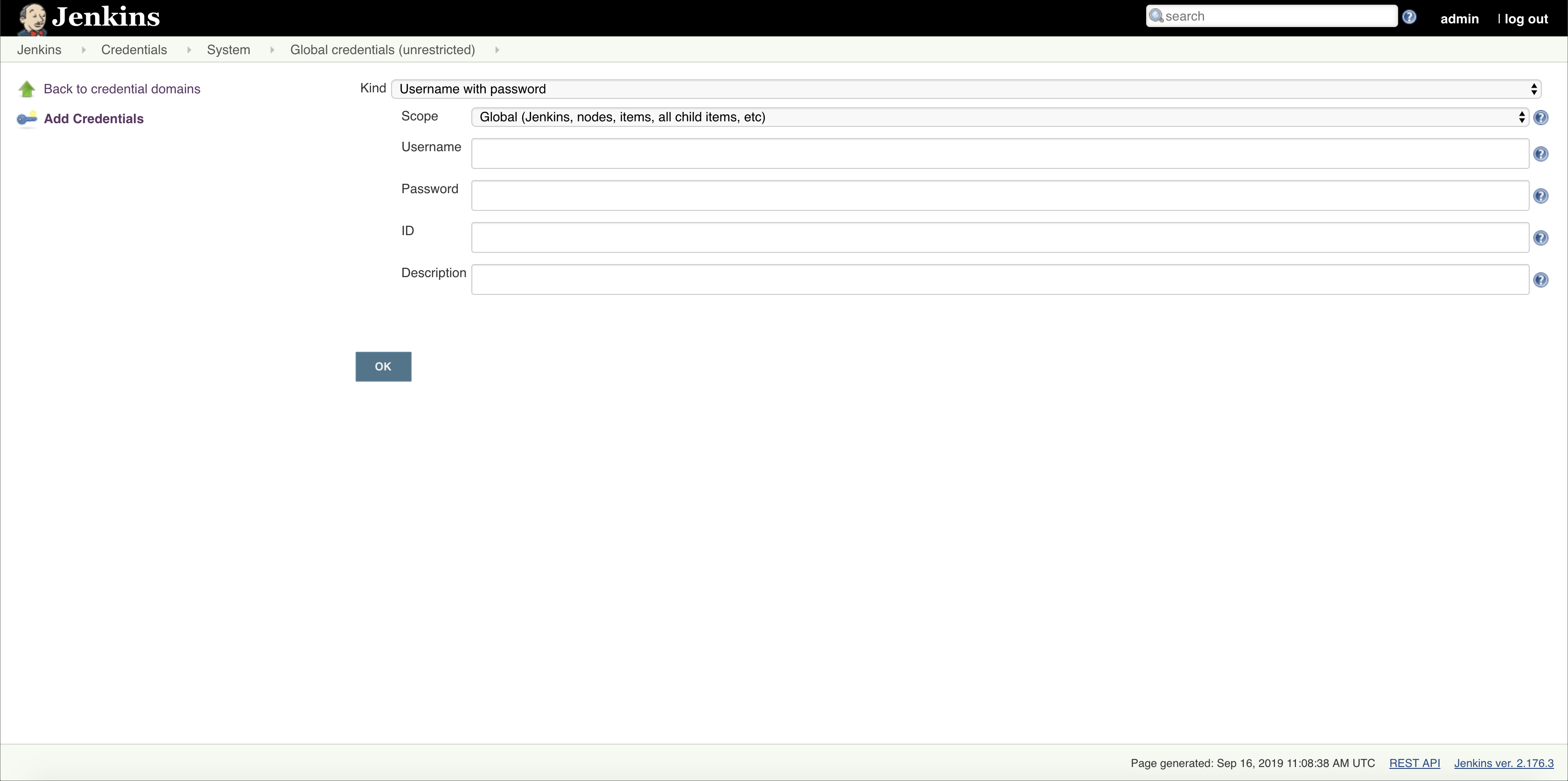
- Click Add Credentials. Enter the credentials of the GitHub repository, and click OK.
- Repeat the previous step to add credentials to the BitBucket repository, Skyhigh Security Skyhigh CASB application.
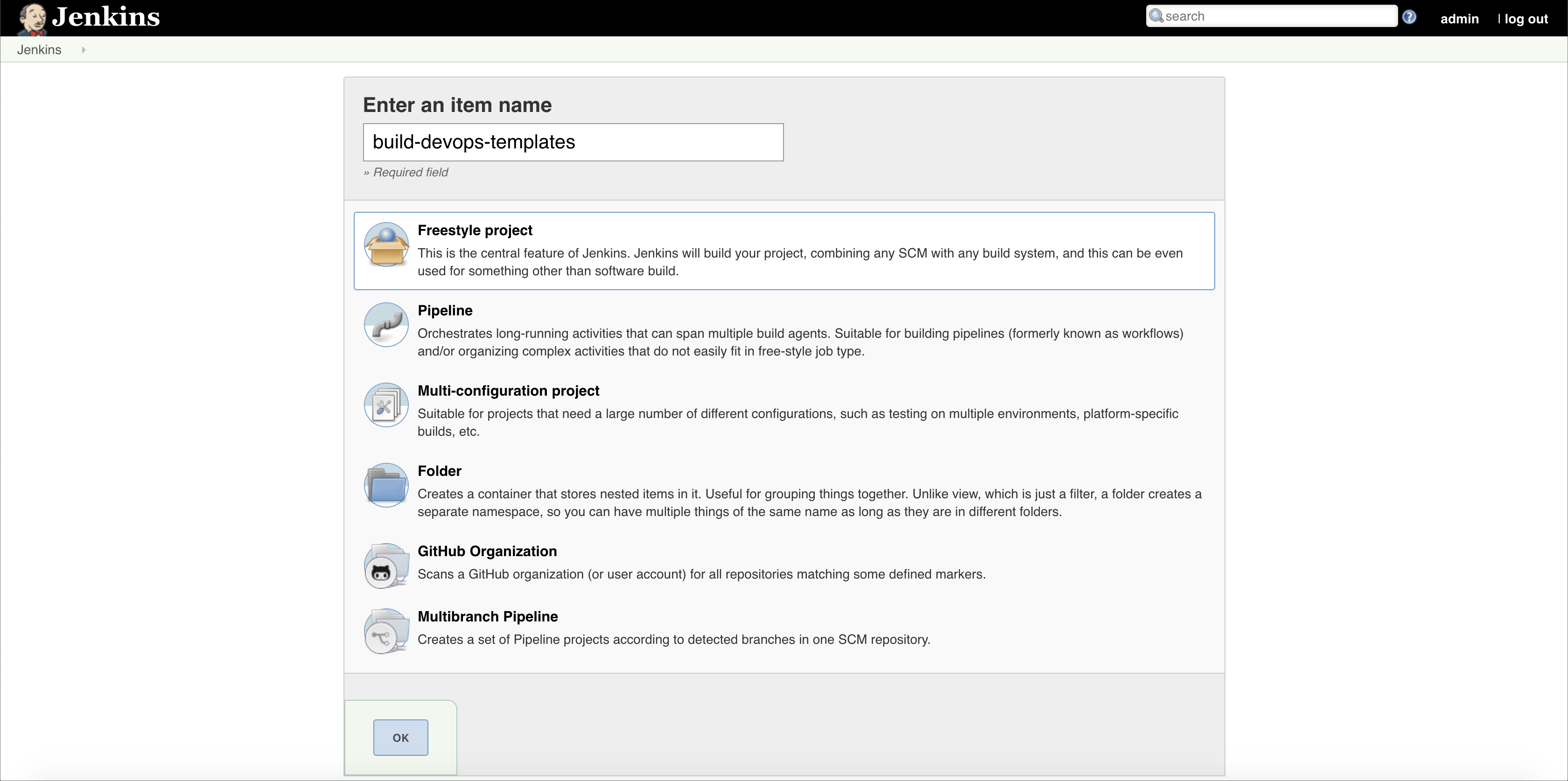
- Go to the Jenkins homepage. Click Create new jobs > Freestyle Project.
- Enter a name for the job, and click OK.
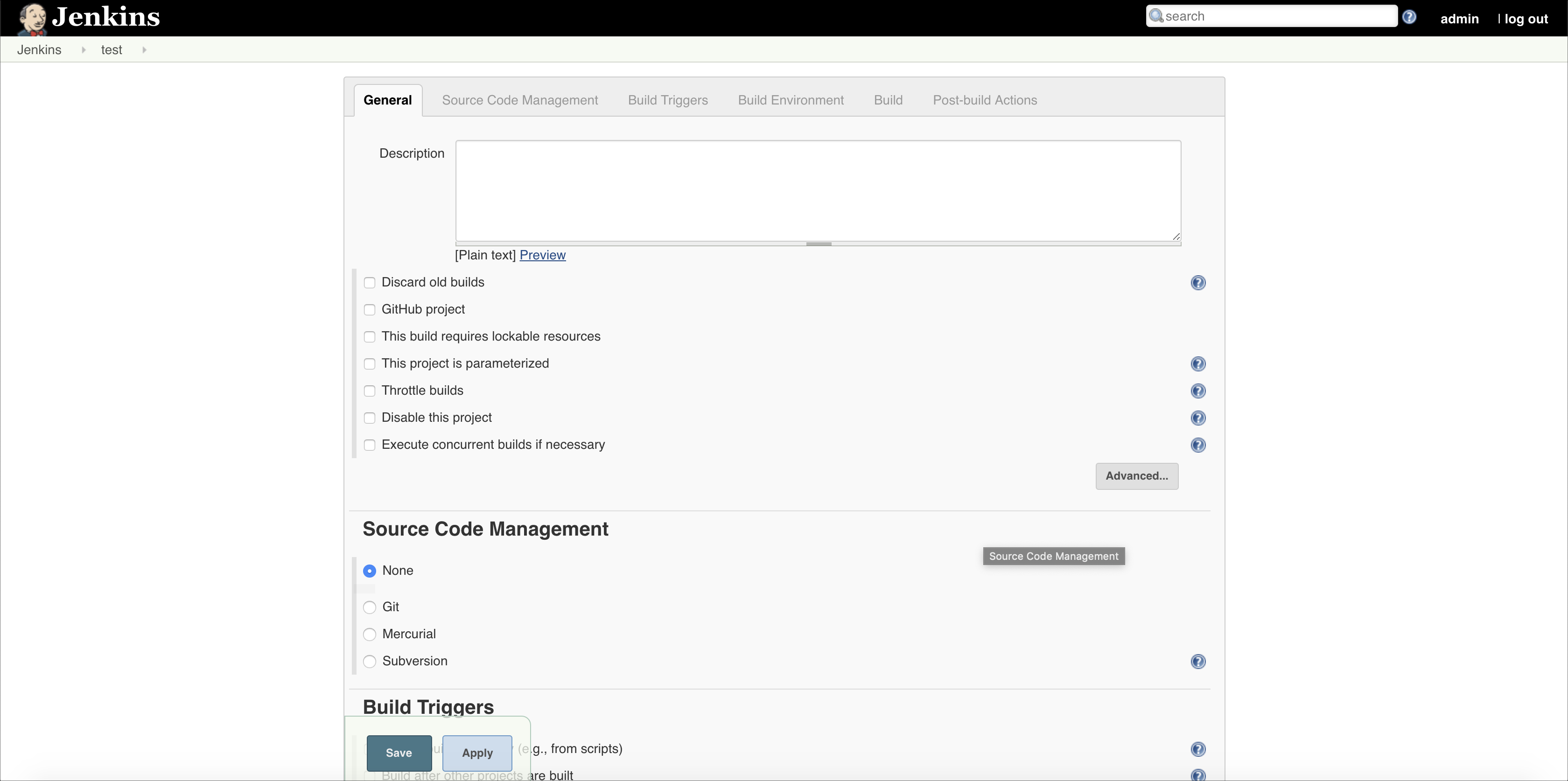
- Click Configure on the job page. You see the following page:
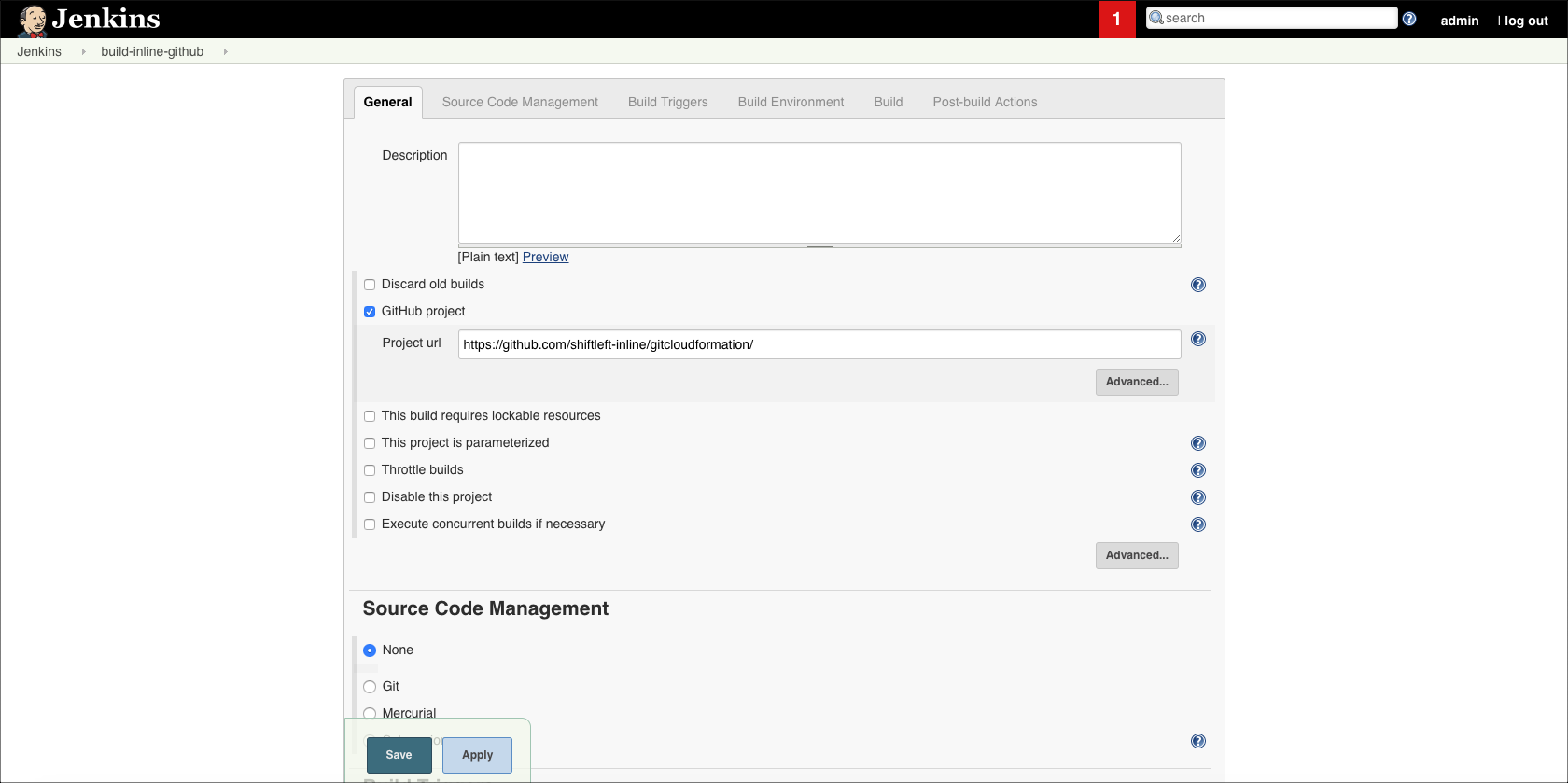
- For GitHub, under the General tab, select the option GitHub project and the GitHub repository URL as shown:
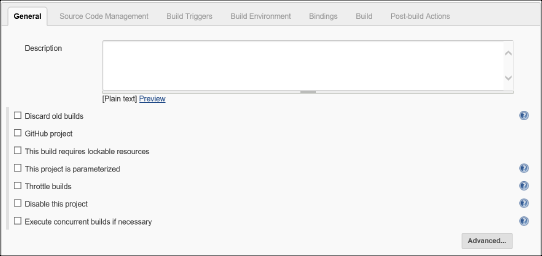
- For BitBucket, under the General tab, don't select anything.
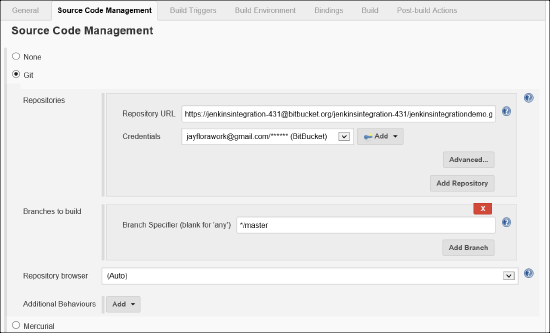
- Select Git under Source Code Management and enter the repository URL and select the repository credentials from the menu.
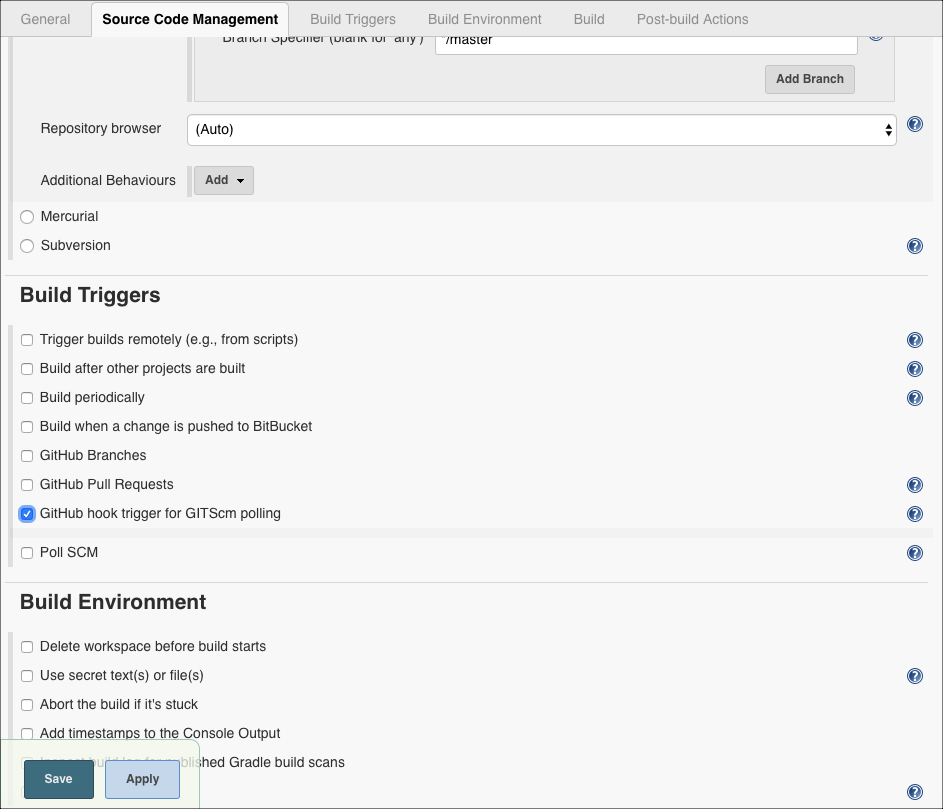
- For GitHub, select the GitHub hook trigger for GITScm polling under the Build Triggers section as shown:
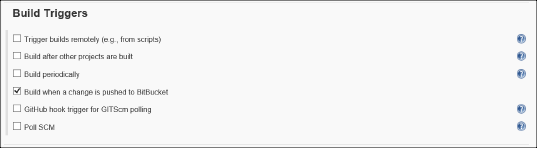
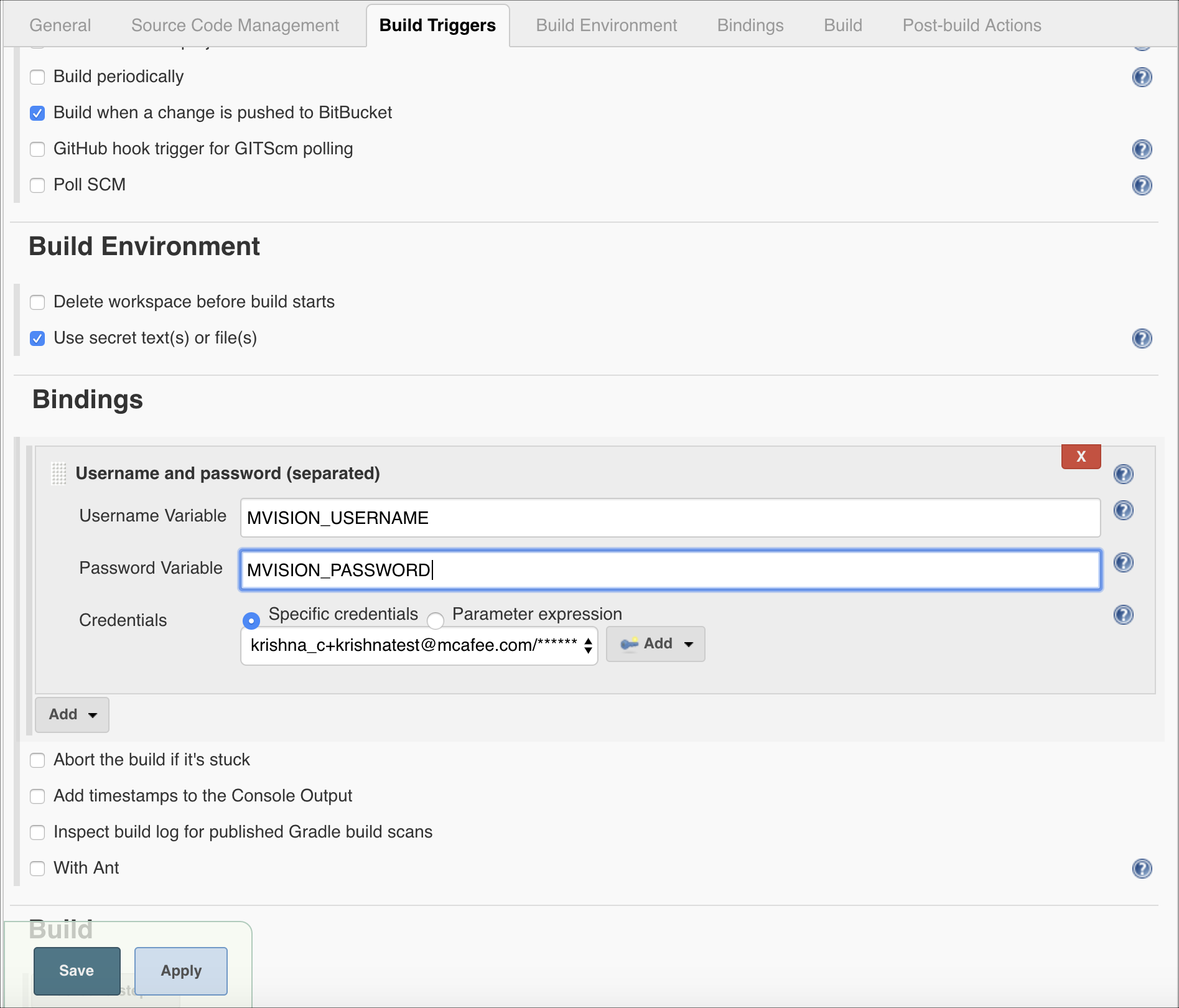
- For BitBucket, under Build Triggers select Build when a change is pushed to Bitbucket.
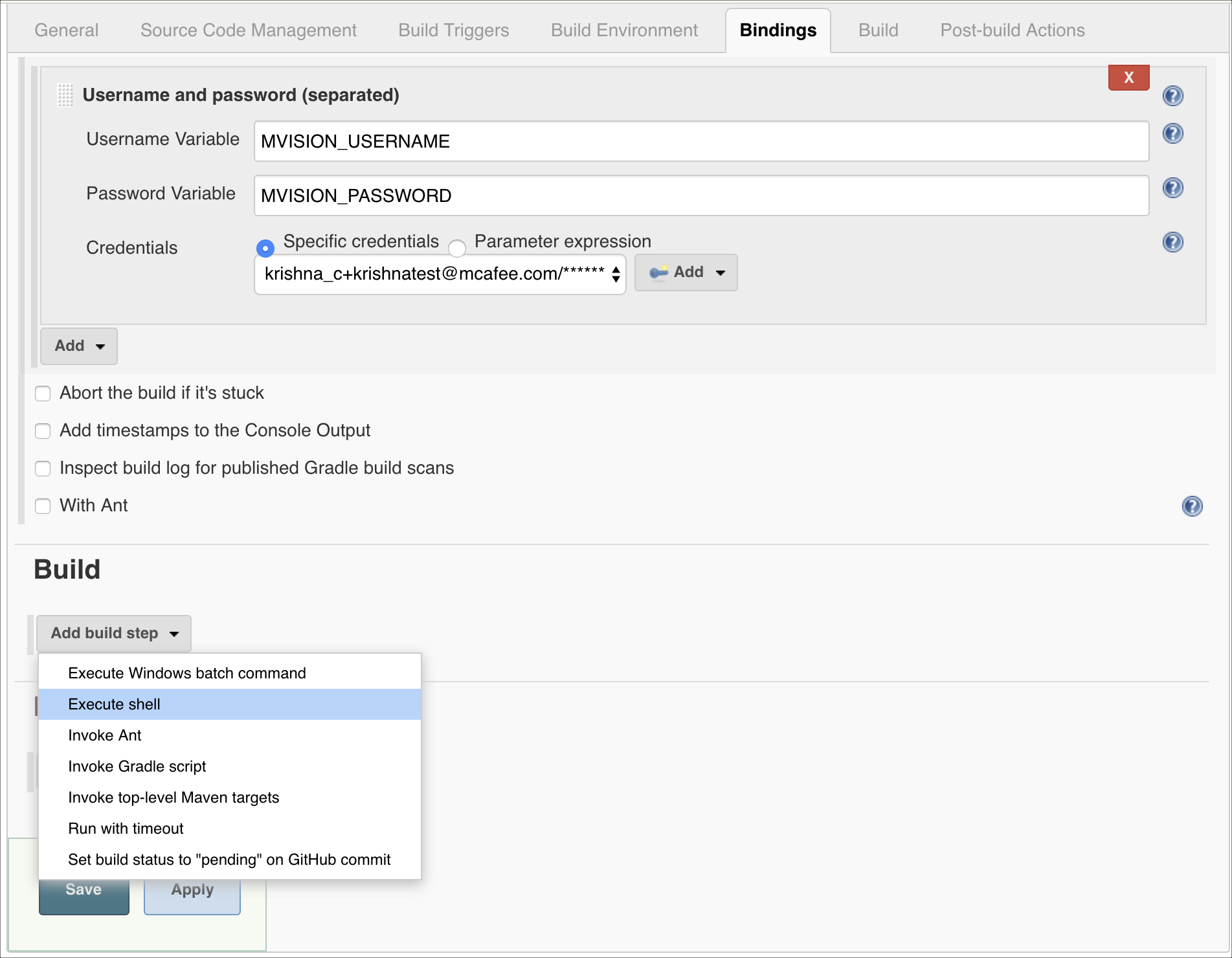
- Select Use secret test(s) or file(s) under the Build Environment section. Click Add under Bindings section, Select Username and password (separated) as shown.
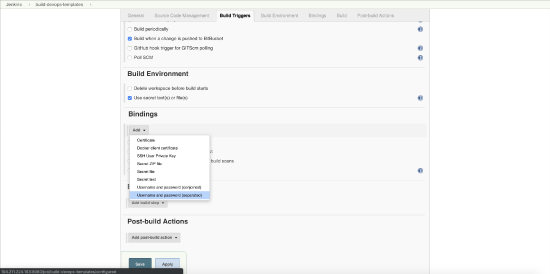
- Enter Skyhigh CASB_USERNAME in the Username variable text box and Skyhigh CASB_PASSWORD in the Password Variable and select the Skyhigh CASB credentials from the menu.
- For Ubuntu VM, In the Build section, click Add build step and select Execute Shell and paste the below shell script in the text area then click Save.
# The below statement needs to be executed to find the list of files changed in the last push to the repo
git log HEAD -1 --name-only --oneline --pretty="format:" > shift_left_${BUILD_NUMBER}.txt
# For all files to be evaluated, run below instead
# find ./ -type f \( -iname \*.yaml -o -iname \*.yml -o -iname \*.tf -o -iname \*.json\) > shift_left_${BUILD_NUMBER}.txt
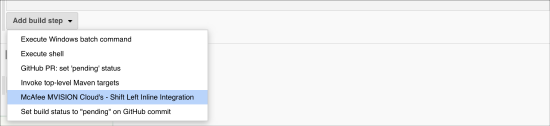
- In the Build section, click Add build step and select Skyhigh CASB - Shift Left Inline Integration.
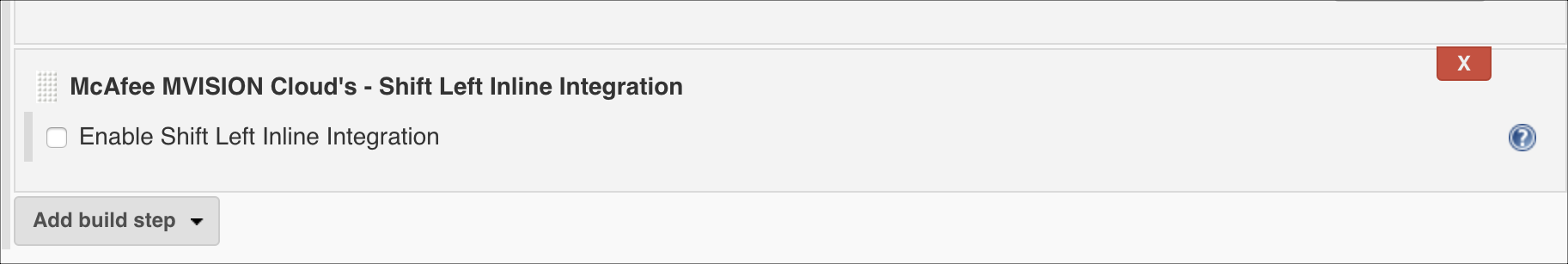
- From the following option in Jenkins, select Enable Shift Left Inline Integration.
- From the menus, select the cloud service provider for DevOps templates you want to evaluate, and select your Skyhigh CASB environment.
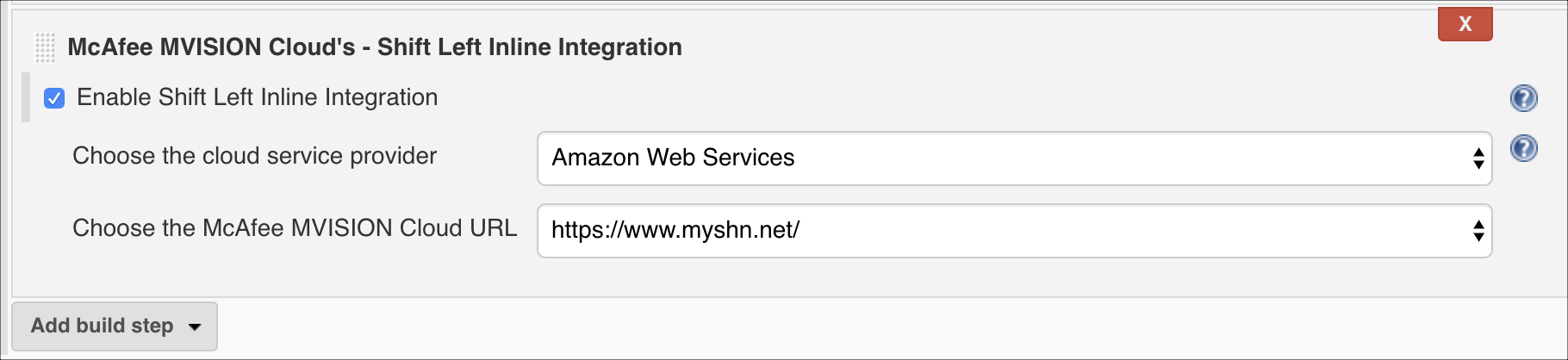
- Click Save/Apply.
Configure GitHub
To configure GitHub:
- Select the repository you want to integrate in GitHub, and navigate to Settings > Webhooks > Add Webhook. You see the Add webhook page.
- Populate the following values:
- Payload URL with value <<jenkins-url/github-webhook/>>. Use the public IP of Jenkins.
- Select the content type as application/json.
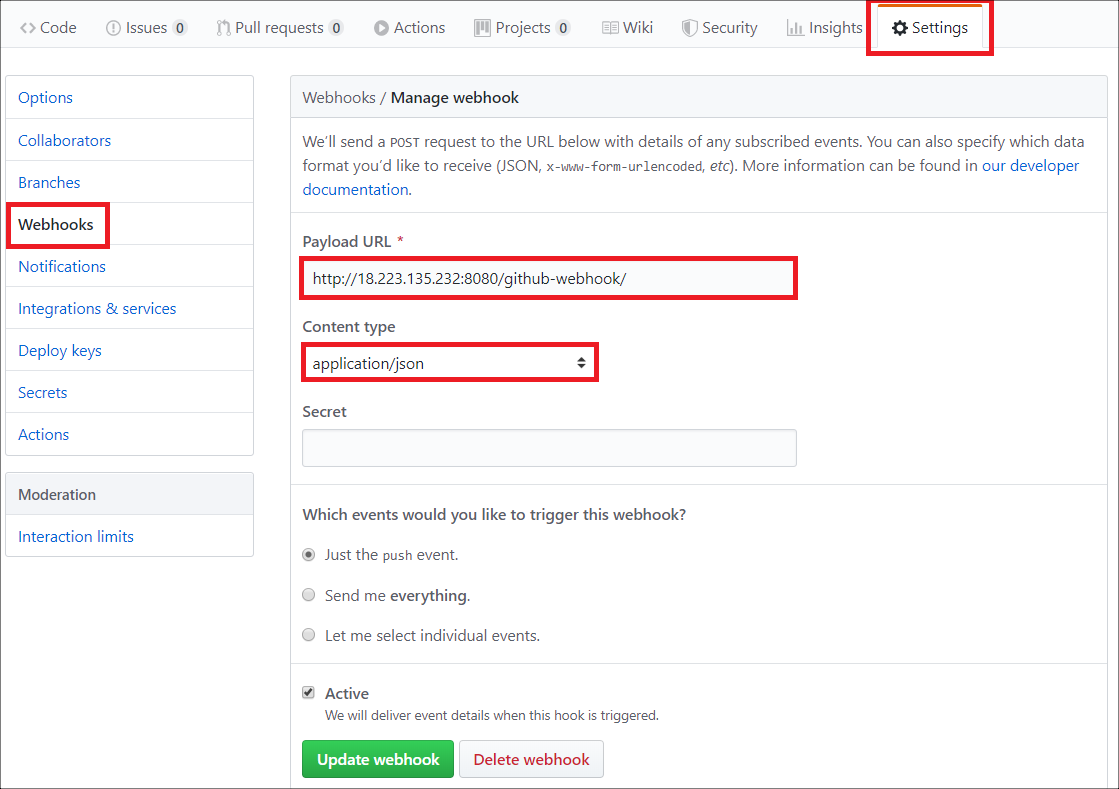
The GitHub and Jenkins integration with Skyhigh CASB inline plugin is complete.
Any time you push to the GitHub repository triggers a build in Jenkins, which in turn performs the Skyhigh CASB integration to check for vulnerabilities present in the DevOps template pushed to the repository.
Configure Bitbucket
To configure Bitbucket:
- In Bitbucket, select the repository you want to integrate.
- Go to Settings > Webhooks > Add Webhook. The Add new webhook page opens.
- Add a Title, and enter the Jenkins URL bitbucket-hook/.
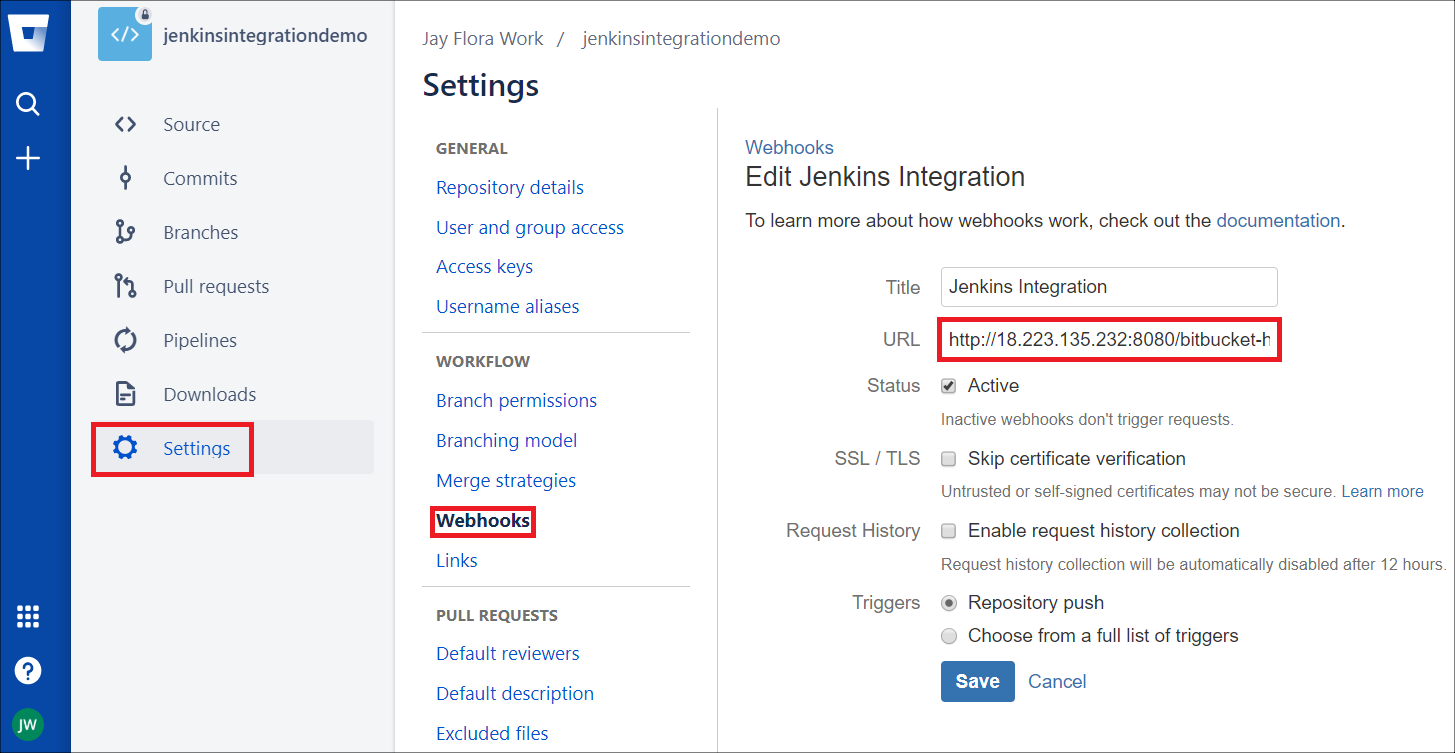
- Click Save.
The integration of Bitbucket and Jenkins with inline API is complete.
Any push to the Bitbucket repo triggers a build in Jenkins, which in turn calls the Skyhigh CASB inline APIs to check for vulnerabilities present in the DevOps template committed in Bitbucket.
