Associate Lambda-based Policy to a Custom AWS Service
As a Security Operations Admin, you can secure AWS services across your organization. When these services run critical workloads, you need instant visibility to monitor the services. Skyhigh CASB can configure the accounts to support near real-time monitoring. If Near-Real-Time (NRT) monitoring is enabled, Skyhigh CASB reports misconfigurations in under five minutes.
To accomplish this, associate a Lambda-code to a custom policy that is applicable to one or more AWS services. Then the service can access and leverage NRT monitoring support to detect configuration audit violations.
NOTE: If you've already created a custom policy based on Lambda code, you will need to associate specific AWS services to the policy to allow near real-time evaluation of those policies.
If a policy does not already exist, to set up NRT support for a custom Lambda policy, you will need to create a policy from a policy template.
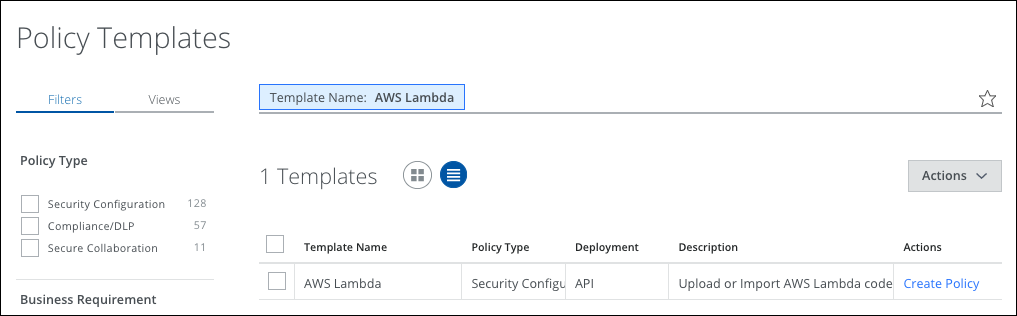
- Go to Policy > Policy Templates.
- Search for the AWS Lambda policy template. Click the List icon to display results.
- Select the AWS Lambda template and click Actions > Create Policy.
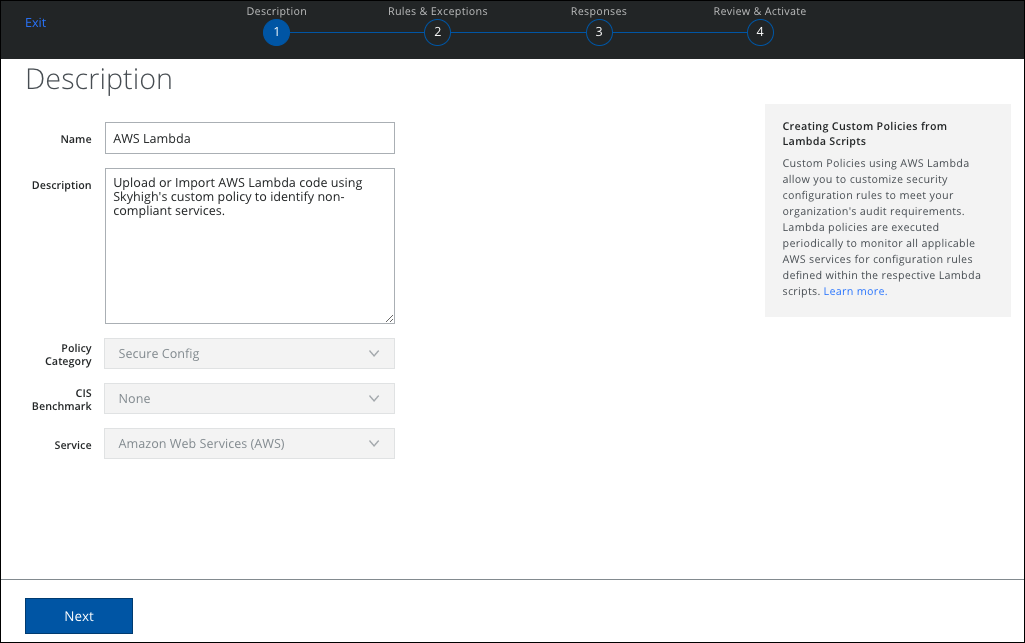
- On the Description page, enter a name for the policy, (for example, AWS Lambda), then click Next.
- On the Rules for AWS Lambda page, select H, M, or L to generate a High, Medium, or Low severity incident.
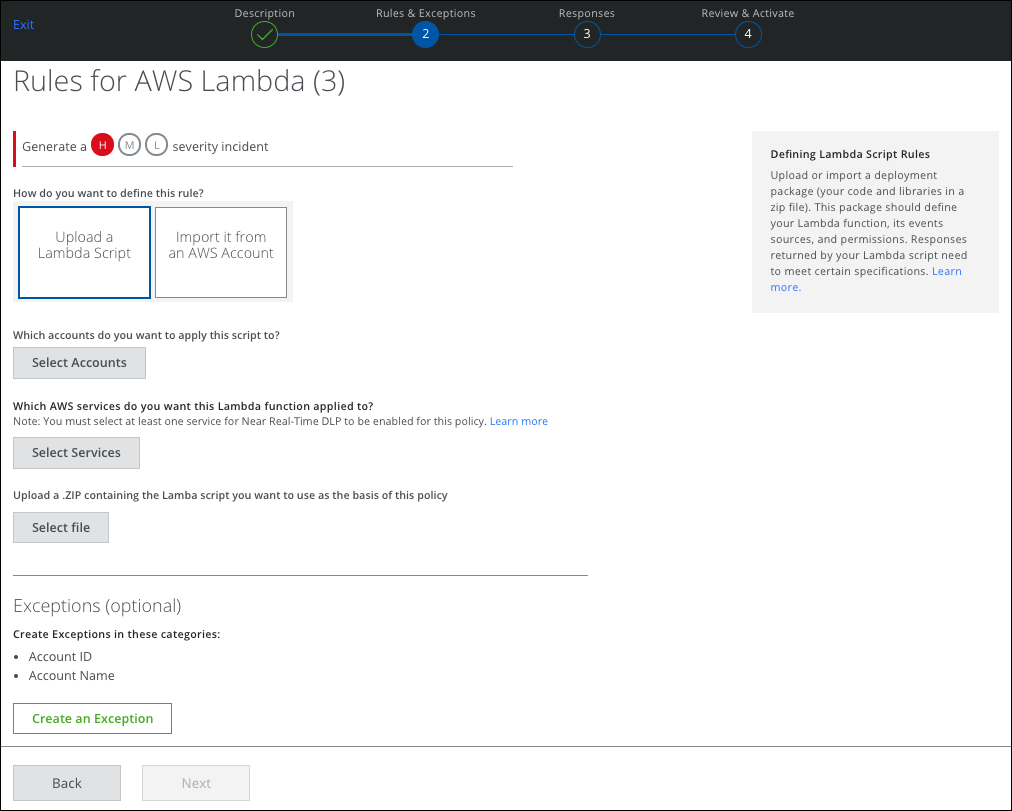
- To upload a Lambda script that is associated with a specific AWS service, select one of the following:
- Upload a Lambda Script
- Import it from an AWS Account
- Select Accounts. Click to select the accounts to apply this script.
- Select Services. Click to select the AWS Services you want this Lambda function applied to.
NOTE: You must select at least one service for Near Real-Time DLP to be enabled for this policy. - Select File. Click to upload a ZIP file containing the Lambda script you want to use as the basis of this policy.
- Create an Exception. Click to create exceptions in the available categories.
- Click Next.
- Define Responses.
- Click Next.
- Review your policy and activate it.
