Configure the Cloud Proxy Servers
To redirect web traffic, configure the gateway list and rules. Configure Skyhigh Security WSGS as the gateway and provide host name in the c<customer_id>.wgcs.skyhigh.cloud format. Example: c<customer_id>.wgcs.skyhigh.cloud
NOTES:
- Before you can save the policy, you must provide the IP address or host name of at least one gateway and a port number.
- When you enable the Secure Channel option with at least one cloud gateway configured in the list, Client Proxy ignores on-premise proxy servers and considers only gateways configured in the list. Depending on the availability of a gateway and port, Client Proxy applies redirect, block, or fallback (Allow connection without Secure Channel) option. Gateway with domain like c*******.wgcs.skyhigh.cloud is considered as cloud proxy.
Complete the following:
- On the Skyhigh SSE navigation bar, click Settings.
- Select Infrastructure | Client Proxy Management.
- Do one of the following:
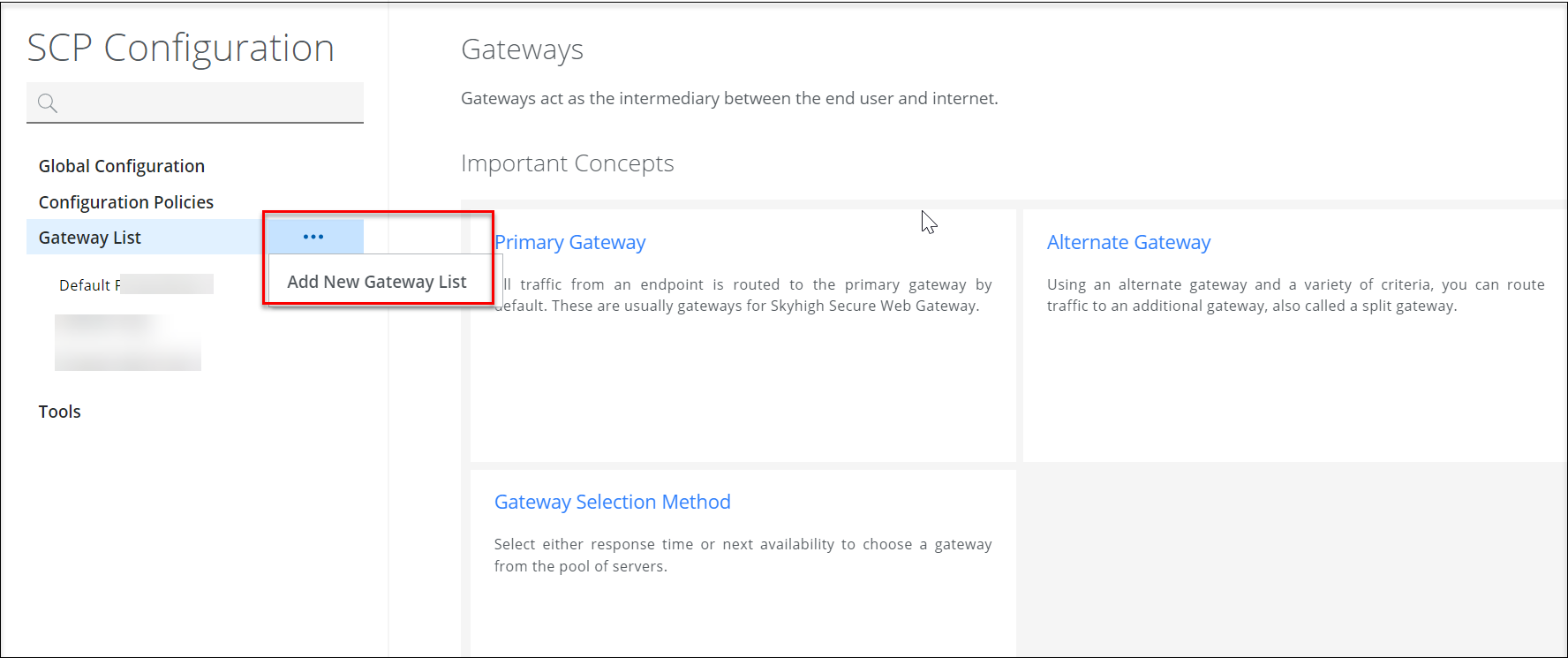
- Go to Gateway List > Add New Gateway List.
- Select a gateway from the Gateway List and click Add Gateway.
- In the Gateway section, complete the following:
- Gateway Hostname or IPv4 Address — Specifies the IPv4 address or host name.
- Listening Port — Specifies the port number of the proxy server.
- Redirect Ports 80 & 443 — Select this checkbox to redirect traffic sent to ports 80 and 443 to the gateways.
- Non-HTTP/HTTPS Redirected Ports — Specifies the port numbers of protocols other than HTTP/HTTPS whose traffic you want redirected. Verify that the gateway supports these protocols. You can enter up to 1024 characters in this field.
- + — Click this to add another gateway.
- To specify how the software selects a gateway from the list, select an option in the Gateway Selection Method section:
- First Available — The software selects the next gateway from the list that you configure.
- Fastest Response Time — The software selects the next gateway from the list that it maintains, which is based on response time.
-
NOTE: While using the Secure Channel feature, the Automatic Switch Over is not applicable for a gateway list. - Click Save.
Additionally, you can do the following on the Admin tab:
- Uncheck (clear) the Bypass all Gateways for Local Traffic (10.xxx, 192.168.xx, ...) check box to redirect all traffic, including traffic sent to local addresses inside your organization's subnet network, to a gateway. You can configure an IP address, IP address range, subnet, or CIDR. For example, 192.168.1.1, 172.31.255.10-172.31.255.20, 10.50.0.0/255.255.128.0 or 10.50.0.0/17.
- To configure other ports to redirect traffic as HTTP/HTTPS traffic, select the List of configured ports to redirect as HTTP/HTTPS traffic check box. For more information, see Configure Ports to Redirect as HTTP/HTTPS Traffic.
- To block traffic:
- Select the Primary gateway is unreachable check box to block traffic on the configured ports if none of the primary gateway is unreachable. When you do so, all traffic to the configured ports and default ports 80 and 443 are blocked.
- Select Block Traffic on configured Ports until SCP is Ready to protect the endpoint while Client Proxy is starting. All traffic to the configured ports and default ports 80 and 443 is blocked from the time the user has internet access until Client Proxy exits bypass mode and starts redirecting traffic.
- Select Traffic is IPv6 to block all IPv6 traffic and web browsers to fall back to IPv4 traffic.
- Select Mutual Authentication with primary gateways fails to make sure that Client Proxy only redirects web requests when it can authenticate the gateway.
- Select UDP Traffic on Ports 80 and 443 to block UDP traffic for IPv4 and IPv6.
