Configure the Bypass List
The bypass list allows you to configure domain names or network addresses, ports, and process names to bypass the proxy and steer traffic to Cloud Firewall. You can view the bypass list and add, edit, or remove items from the list as needed.
Client Proxy policy allows traffic that matches the items on the bypass list bypasses the primary gateway and go directly to the Internet. The servers in the alternative gateway are not affected by the bypass list.
You can check the firewall rules section on the application site to know the list of domains, IP addresses, and process names of the applications to be added to the bypass list.
To configure Client Proxy policy to bypass traffic:
- In Skyhigh, go to Settings > Infrastructure > Client Proxy Management.
- In the policy tree, select Configuration Policies.
- Click Create New Policy or select a policy from the policy tree.
- Click the Proxy Bypass tab.
- Complete the following:
- To add domain names or IP addresses, do one of the following:
- Select Bypass all proxies for traffic to these domains to open Bypass traffic to the domains.
- Select Add Domain > Add Inline.
- Domain — Enter the domain names of the application.
- Comment — Enter additional information.
- + — Click to add another IP address.
Note: Use the Import CSV option to import the domain list.
- Select Add Domain > Add Inline.
- Select Bypass all proxies for traffic to these destination IP addresses to open Bypass traffic to the IP addresses.
- Select Add IP Address > Add Inline.
- IP Address — Enter the IP address of the applications. For example, 3.21.137.128/25
- Comment — Enter additional information.
- + — Click to add more IP addresses to the list.
Note: Use the Import CSV option to import the IP address list.
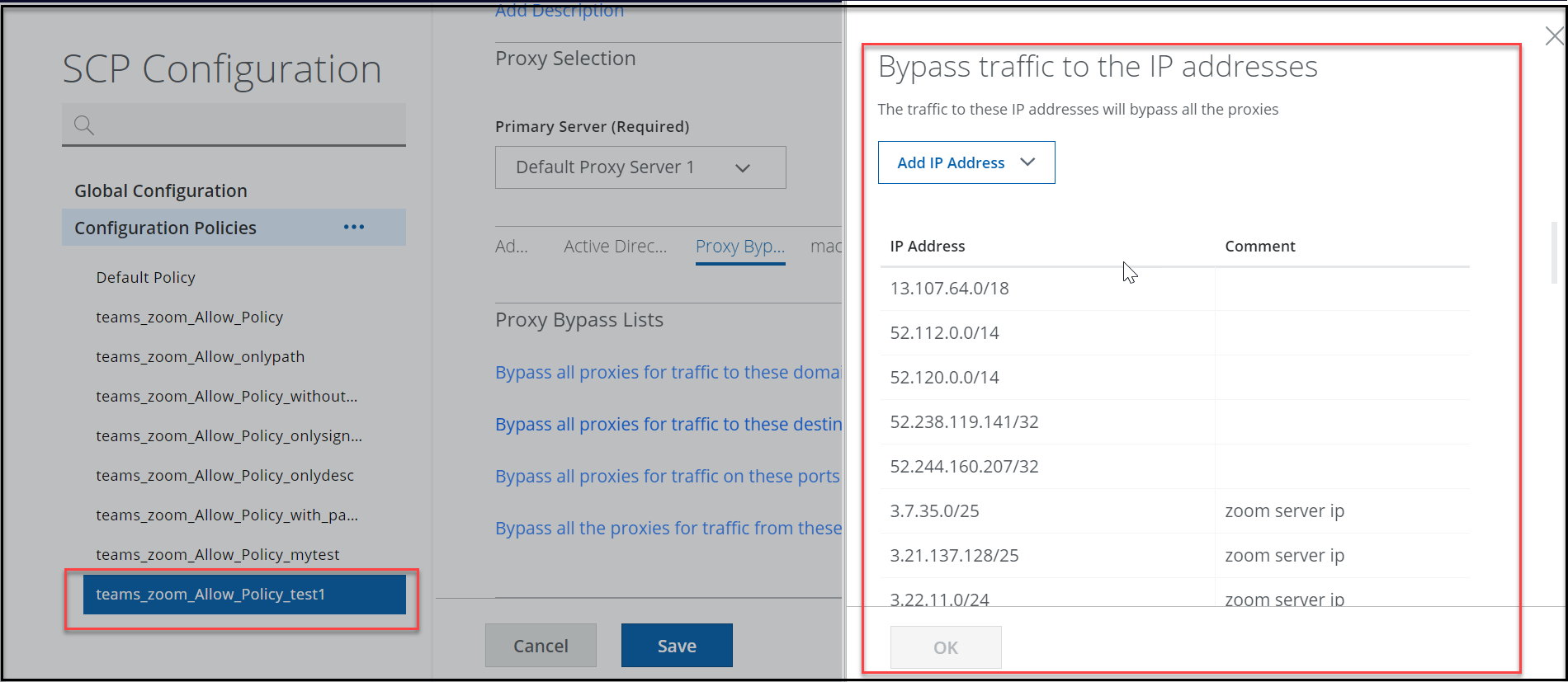
- Select Add IP Address > Add Inline.
- Select Bypass all proxies for traffic to these domains to open Bypass traffic to the domains.
- Select Bypass all the proxies for traffic from these processes to open Bypass traffic to the processes.
- Select Add Process > Add Inline.
- Process — Enter the process from which the traffic is bypassed. For example, zoom.exe. teams.exe
- Comment — Enter additional information.
- + — Click to configure another process.
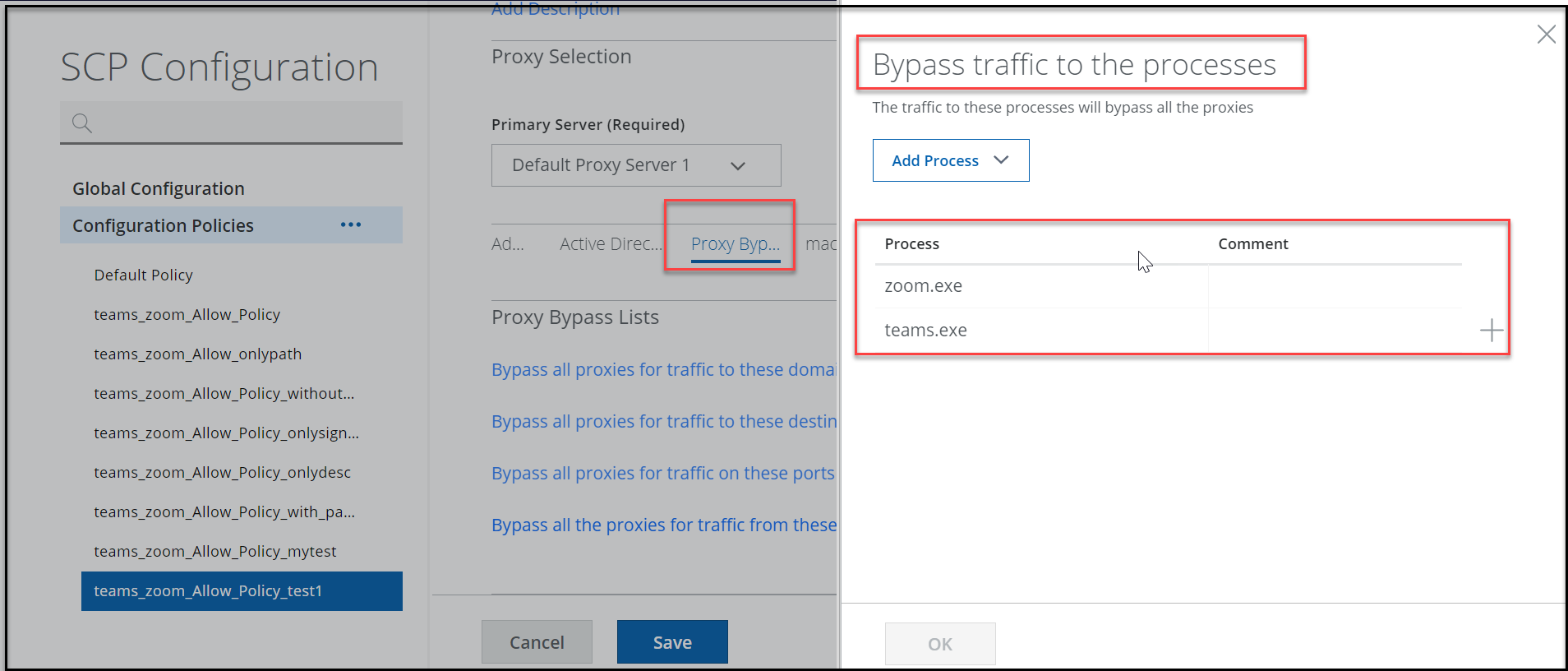
- Select Add Process > Add Inline.
- To add domain names or IP addresses, do one of the following:
- Click Save.
You can publish saved changes to the cloud now or keep working and publish later.
